Sponsored by LastPass
Sponsored by Security Compliance Corporation
First National Bank Streamlines Identity Governance with Access Auditor
Sponsored by Security Compliance Corporation
Case Study | How to Automate User Access Reviews
Sponsored by HelpSystems
Classification By Design: The Foundation Of Effective Data Protection Compliance
Sponsored by ServiceNow
A Secure Platform to Transform Financial Services
Sponsored by Imperva
The Road to Compliance: Steps for Securing Data to Comply with the GDPR
Sponsored by Imperva
A Closer Look at CCPA
Sponsored by Skybox Security
Stronger Security Through Context-aware Change Management: A Case Study
Sponsored by Skybox Security
Rule Life Cycle Management
Sponsored by Fourthline
Glocal KYC: not all EU countries are created equal
Sponsored by Clearwater Compliance
From Risk Analysis to Risk Reduction: A Step-By-Step Approach
Sponsored by Fourthline
KYC Remediation: Mistakes and Best Practices
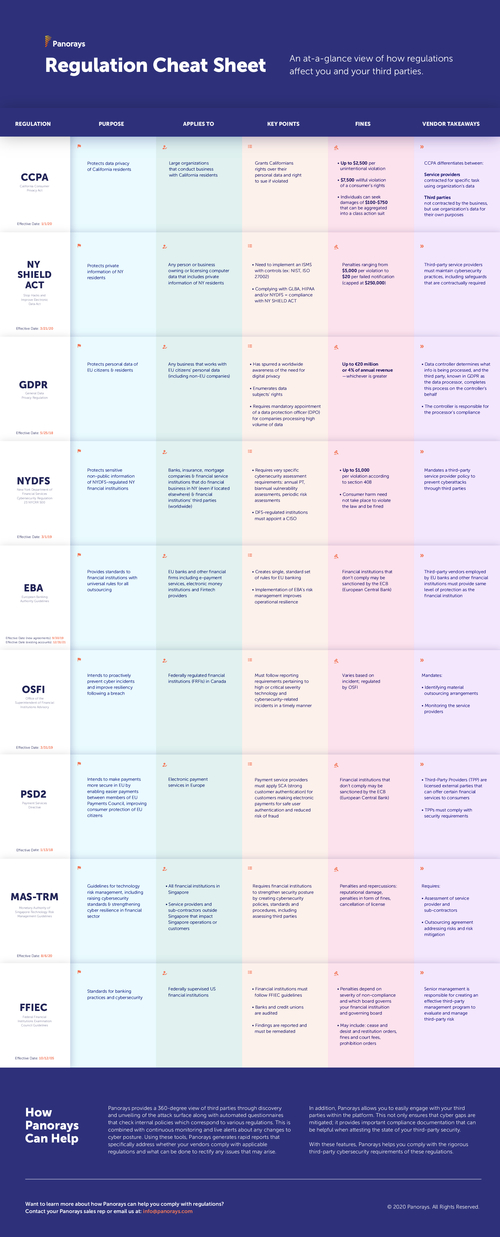
Sponsored by Panorays
How to Create Scalable Vendor Security Questionnaires
Sponsored by Panorays