Sponsored by Cloudera
Sponsored by AWS
Amazon GuardDuty Security Review
Sponsored by AWS
Achieve Machine Learning Results Faster
Sponsored by AWS
Creating a Culture of Security
Sponsored by AWS
Achieve Machine Learning Results Faster
Sponsored by AWS
Innovate By Migrating to the Most Secure Cloud
Sponsored by ActZero
Why You Need a Modern Regulatory Framework
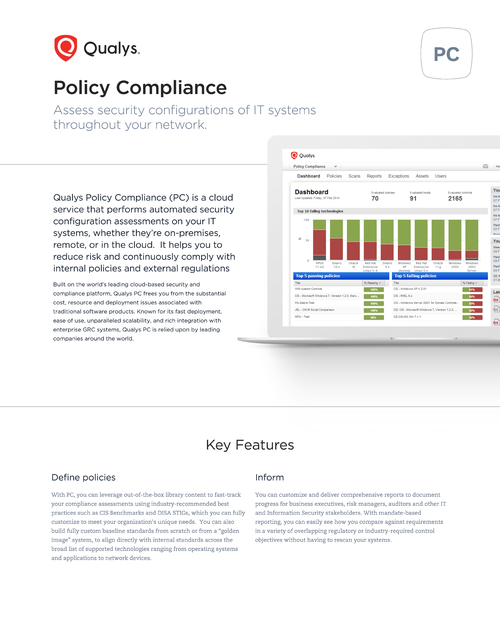
Sponsored by Qualys Inc.
Cloud Based Security & Policy Compliance
Sponsored by Red Hat
Trusted Software Supply Chain
Sponsored by Red Hat
A Guide to Improving Compliance with Network Automation Technology
Sponsored by Immersive Labs
eBook | The Ultimate Cyber Skills Strategy Cheat Sheet
Sponsored by Imperva
Cyber Security and Compliance Guide for Financial Services
Sponsored by Dtex Systems
Everyone as a Trusted Insider: An Intelligent Replacement for Employee Monitoring
Sponsored by Dtex Systems