Sponsored by ManageEngine
Sponsored by ManageEngine
Ransomware – COVID -19 Caused Mutations and the Ultimate Guide for Protecting your Remote Workforce
Sponsored by Censys
US Critical Infrastructure Report: Oil & Natural Gas Pipeline
Sponsored by Censys
Attack Surface Management Buyer's Guide
Sponsored by Proofpoint
The Business Email Compromise Handbook
Sponsored by Okta
Safeguarding Unemployment Insurance Benefits from Fraud
Sponsored by Okta
The 3 Tenets of Enabling a Remote Government Workforce
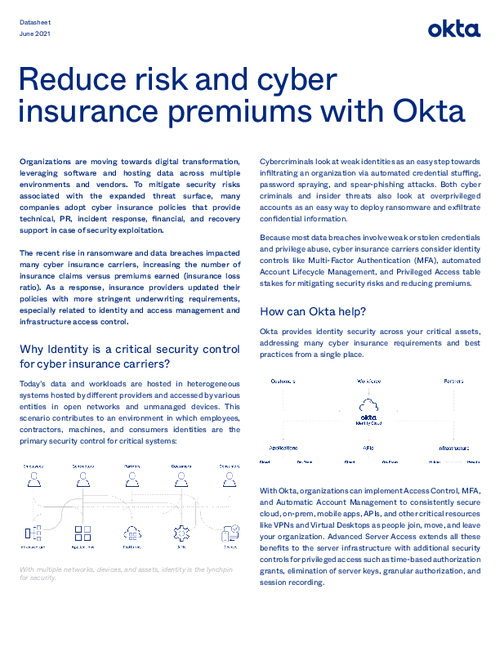
Sponsored by Okta
Reduce risk and cyber insurance premiums with Okta
Sponsored by Cribl
Observability Pipelines for Dummies
Sponsored by Cribl
FINRA Levels Up Their Data Game Without A Steep Learning Curve
Sponsored by Cribl