Sponsored by DTEX Systems
Sponsored by Gigamon
ThreatINSIGHT Via Network Detection and Response
Sponsored by Orca Security
The Ultimate Guide to: AWS, Azure, and GCP Cloud Asset Visibility
Sponsored by Orca Security
SideScanning - Inside the Engine that Powers Orca Security
Sponsored by Zoho Corp - ManageEngine
Combating Hacking Techniques: How to Defend Against DDoS, Ransomware, and Cryptojacking
Sponsored by Splunk
Beginners Guide to Observability
Sponsored by Splunk
The Essential Guide to Container Monitoring
Sponsored by Globalsign
Certificate Lifecycle Management Just Got More Strategic
Sponsored by Splunk
GigaOm Cloud Observability Report
Sponsored by Splunk
A Beginner's Guide to Kubernetes Monitoring
Sponsored by Splunk
The Guide to Modern APM: Essentials for Your Cloud-native Journey
Sponsored by Splunk
5 Things to Consider When Choosing an APM Tool
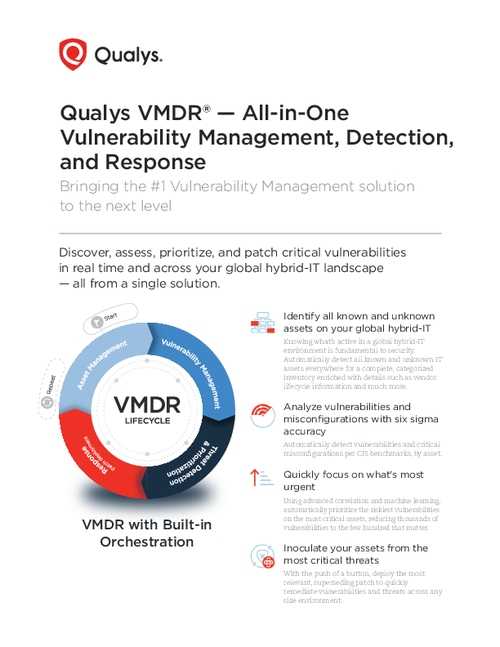
Sponsored by Qualys Inc.
An All-in-One Vulnerability Management, Detection, and Response Solution
Sponsored by Expel
MITRE ATT&CK in Amazon Web Services (AWS): A Defender's Cheat Sheet
Sponsored by TrueFort