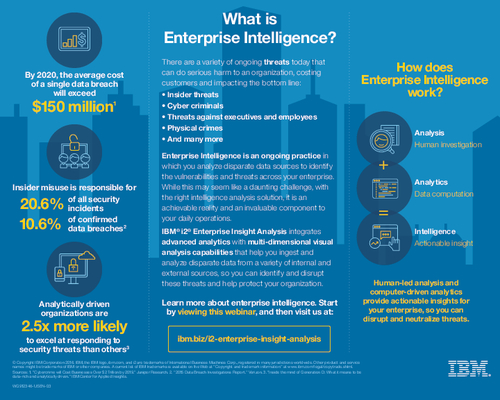
Sponsored by IBM
Sponsored by Entrust Datacard
Top 5 Reasons Why Mobile will Transform Enterprise Authentication
Sponsored by Kaspersky Lab
Forward Facing Fraud Prevention
Sponsored by FireEye
Make Threat Intelligence Work for You
Sponsored by Kaspersky Lab
Kaspersky Lab's New Focus on Fraud Prevention
Sponsored by Forcepoint
Securely Access Business Applications with Visibility and Control; A Case Study
Sponsored by FireEye
How to Make Threat Intelligence Work for You
Sponsored by IBM
Counter and Mitigate More Attacks with Cyber Threat Hunting
Sponsored by Red Hat
How to Modernize the Federal Enterprise with Open Hybrid Cloud
Sponsored by Trend Micro
Securing the Server Compute Evolution: Hybrid Cloud Has Transformed the Datacenter
Sponsored by Bottomline
Banks Verses Payment Fraud; Defend Your Digital Payment Channel with a Full-Court Press
Sponsored by Forcepoint
9 Steps to Building an Insider Threat Defense Program
Sponsored by Forcepoint
Federal Agencies Make the Case for Modern Network Security Operations
Sponsored by IBM