Sponsored by Kroll Advisory Solutions
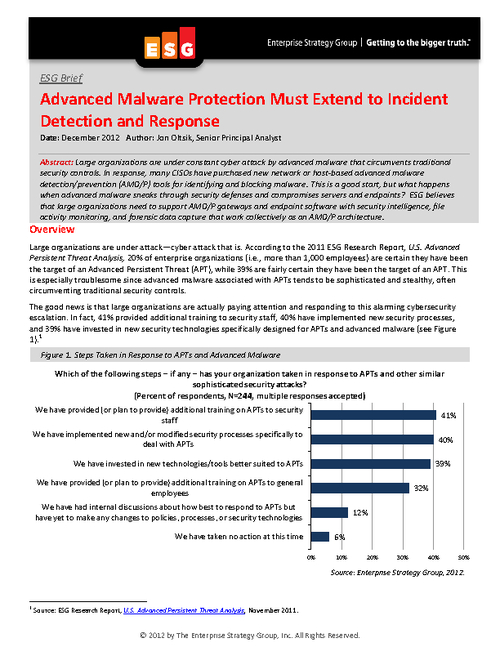
Sponsored by Sourcefire Network Security
What's Your Organization's Plan When Malware Sneaks in?
Sponsored by Kroll
Kroll Advisory Solutions 2013 Cyber Security Forecast
Sponsored by SpectorSoft Corporation
Six Obvious Threats to Data Security You Haven't Really Addressed
Sponsored by Dell SecureWorks
12 Things Effective Intrusion Prevention Systems Should Do
Sponsored by RSA, The Security Division of EMC
Split to Secure: New Data Theft Prevention Techniques
Sponsored by ProtectMyDatabase.com
Mitigating Loss: Following the Data is Essential
Sponsored by Experian
Risk Management: Cyber Insurance & Your Data Breach Response Plan
Sponsored by Ipswitch File Transfer
Are Employees Putting Your Company's Data at Risk? [eBook]
Sponsored by Dell SecureWorks
How to Defend Against Advanced Persistent Threats
Sponsored by EdgeWave
Cyber Security Essentials for Banks and Financial Institutions
Sponsored by Experian
Security as a Business Risk - How Data Breaches Impact Bottom Lines
Sponsored by Experian
Data Privacy and Trust in the Mobile World
Sponsored by Experian