Sponsored by Binalyze
Sponsored by Palo Alto Networks
The Six Key Requirements of Multicloud Security
Sponsored by Exabeam
2023 Exabeam State of Threat Detection, Investigation, and Response Report
Sponsored by Binalyze
Preparing Your Incident Response Team for Cyber Resilience
Sponsored by Palo Alto Networks
Cybersecurity Checklist: 57 Tips to Proactively Prepare
Sponsored by Palo Alto Networks
Meeting the Mandate: A Proactive Approach to Cybersecurity Compliance and Incident Reporting
Sponsored by Datto
Datto RMM: A Security-First Solution
Sponsored by Exterro
Jumpstarting Digital Forensic Investigations
Sponsored by Palo Alto Networks
The Critical Nature of Incident Readiness and Response
Sponsored by Cyera
How ACV Auctions Uses Cyera to Control Sensitive Cloud Data Exposure
Sponsored by Palo Alto Networks
Preparing for New Cybersecurity Reporting Requirements
Sponsored by Palo Alto Networks
57 Tips to Secure Your Organization
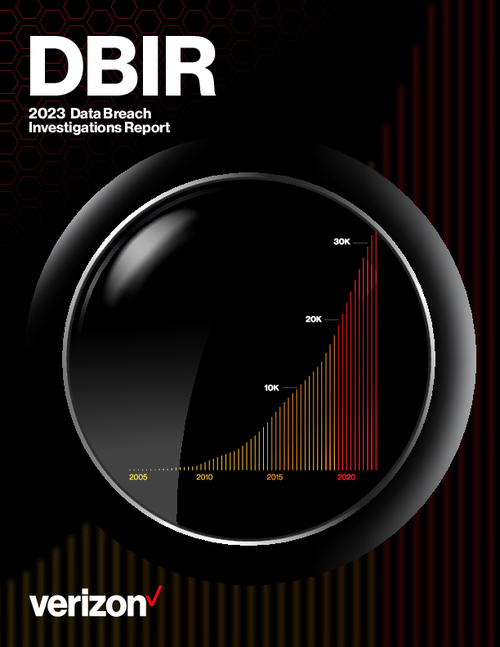
Sponsored by Verizon
2023 Data Breach Investigations Report
Sponsored by Palo Alto Networks