Sponsored by IBM
Sponsored by IBM
Concepts of Intelligence Operations: The New Approach
Sponsored by IBM
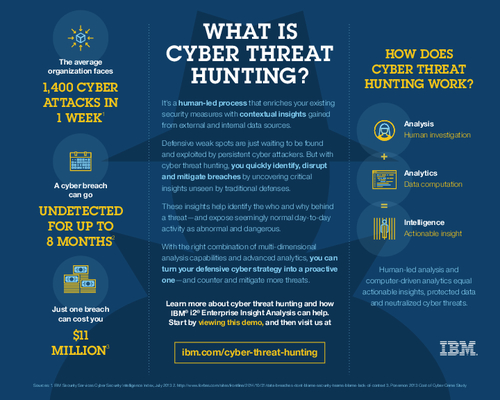
Enterprise Insight Analysis for Cyber Threat Hunting
Sponsored by IBM
How to Use Investigative Analysis to Combat Threat Activity
Sponsored by Digital Guardian
The New 2017 Gartner Magic Quadrant for Enterprise Data Loss Prevention
Sponsored by Barracuda
Office 365 Adoption: Drivers, Risks and Opportunities
Sponsored by iovation
Understanding Today's Customer Authentication Challenges
Sponsored by Akamai
The Case for API Caching
Sponsored by SolarWinds
Find and Secure Your Most Sensitive Data
Sponsored by Bricata
Preventing Attacks from Spreading
Sponsored by Nuance
Banking on Biometrics
Sponsored by IBM
Security in the Age of Open Banking
Sponsored by Carbon Black
The Ransomware Economy
Sponsored by BitSight
GDPR and the Regulatory Impact on Vendor Risk
Sponsored by Carbon Black