Sponsored by IBM
Sponsored by IronNet
A Web of Weak Spots: Securing Your Supply Chain with NDR and Collective Defense
Sponsored by Splunk
The Essential Guide to Data
Sponsored by Splunk
5 Steps to Transform Your IT Organization With AI
Sponsored by OneSpan
Top E-Signature Use Cases In Banking
Sponsored by OneSpan
Banker's Guide to Electronic Signature Delivering an Omnichannel Customer Experience
Sponsored by Nominet
The Risks, Threats and Solutions That Matter Most to Federal Government Agencies
Sponsored by CyberArk
Learning from the Frontlines: 4 Steps to Protect What Attackers are Really After
Sponsored by OneSpan
Account Takeover Fraud How to Protect Your Customers and Business
Sponsored by OneSpan
Digital Account Opening: How to Transform & Protect the Account Opening Journey
Sponsored by Micro Focus
Enable Compliance with Worldwide Regulations at Enterprise Scale
Sponsored by HCL
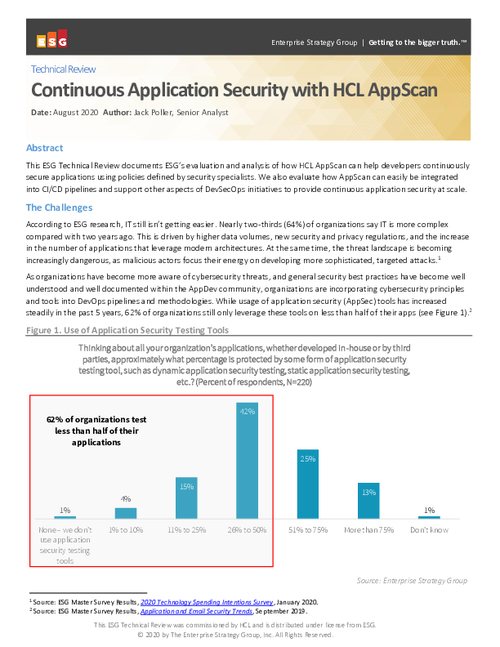
ESG: Continuous Application Security with HCL AppScan
Sponsored by Radware
How to Keep APIs Secure from Bot Cyberattacks
Sponsored by Rapid7
The Four Pillars of Modern Vulnerability Management (French Language)
Sponsored by Rapid7