Sponsored by Ekata
Sponsored by Proofpoint
Be Ready for Ransomware
Sponsored by Proofpoint
Unmasking BEC and EAC
Sponsored by Proofpoint
The Hidden Costs of Free: Are Microsoft 365’s Native Security Features the Value They Seem?
Sponsored by Jumio
eBook | Telehealth: Fighting Fraud With Identity Verification
Sponsored by iboss
Connecting Users to Apps
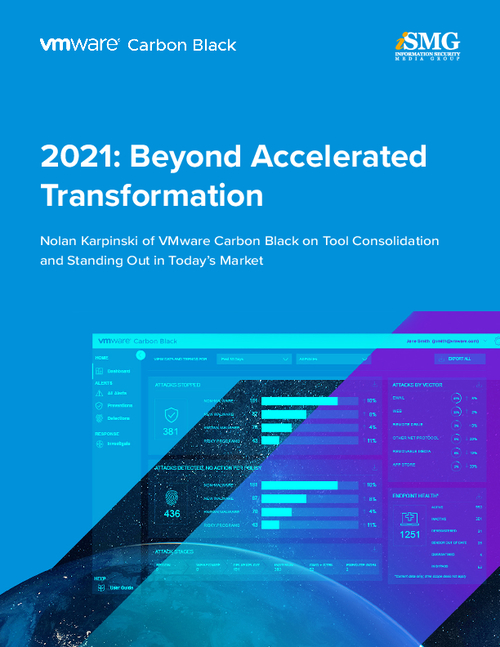
Sponsored by VMware
2021: Beyond Accelerated Transformation
Sponsored by FireEye
M-Trends 2021: FireEye Mandiant Services | Special Report
Sponsored by Watchguard
6 Essential Features of a Modern Firewall
Sponsored by Watchguard
Understanding Cyber Attacks: The Cyber Kill Chain
Sponsored by Cisco
Top cybersecurity trends 2021: Cryptomining
Sponsored by Fortinet
Can You Rely on Microsoft 365 for Email Security?
Sponsored by Fortinet
Security for Microsoft 365: 3 Critical Strategies to Consider
Sponsored by Fortinet