Sponsored by Webroot
Sponsored by Webroot
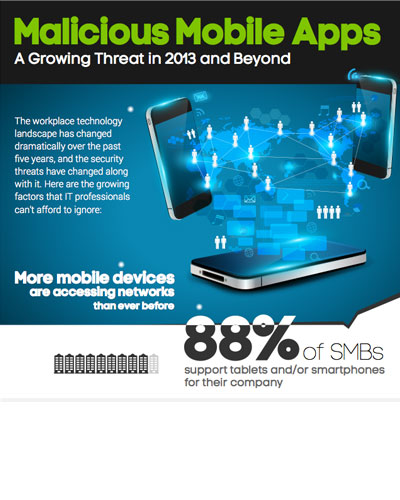
Mobile Browsing - Is Your Company at Risk?
Sponsored by Moka5
BYOD Implementation Guide
Sponsored by ThreatMetrix
Authentication and Fraud Protection for Mobile Devices
Sponsored by Moka5
Essential Technology for Mobile Workforce Security
Sponsored by Ping Identity
Consumer Focused Banking: Implementing Omnichannel Solutions
Sponsored by HP
Top Three Mobile Application Threats
Sponsored by Easy Solutions
Mobile Banking Fraud Prevention Strategy
Sponsored by Accellion
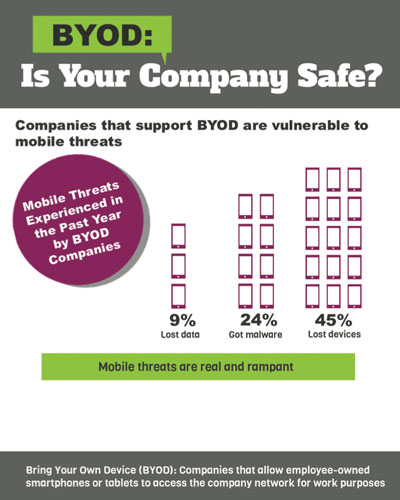
BYOD File Sharing - Go Private Cloud to Mitigate Data Risks
Sponsored by Accellion
5 Best Practices for Secure Enterprise Content Mobility
Sponsored by Accellion
Strategy for Securing Mobile Content: 5 Key Guidelines
Sponsored by Accellion
Mobilize SharePoint Securely: Top 5 Enterprise Requirements
Sponsored by Accellion
Raising the Bar in Secure Cloud-Based File Sharing
Sponsored by Good Technology
Together at Last - BYOD and Solid Security
Sponsored by Good Technology