Sponsored by eSentire
Sponsored by eSentire
Threat Intelligence Spotlight: Hunting Evasive Malware
Sponsored by Red Hat
Define your Path to Security Automation
Sponsored by Red Hat
Ready to Simplify your Security Operations Center?
Sponsored by Red Hat
Security Automation is a Journey
Sponsored by ForeScout
Reducing Risks from IoT Devices in an Increasingly Connected World
Sponsored by ForeScout
Total Visibility: The Master Key to Zero Trust
Sponsored by LastPass
2020 Access and Authentication Trends in the World of Business
Sponsored by Jumio
Remote Onboarding: How Banks are Changing the Game
Sponsored by Illumio
Endpoint Security Effectiveness
Sponsored by Palo Alto Networks
Container Security 101: Understanding the Basics of Securing Containers
Sponsored by Palo Alto Networks
Key Findings: How to Reduce IoT Risks Report 2020
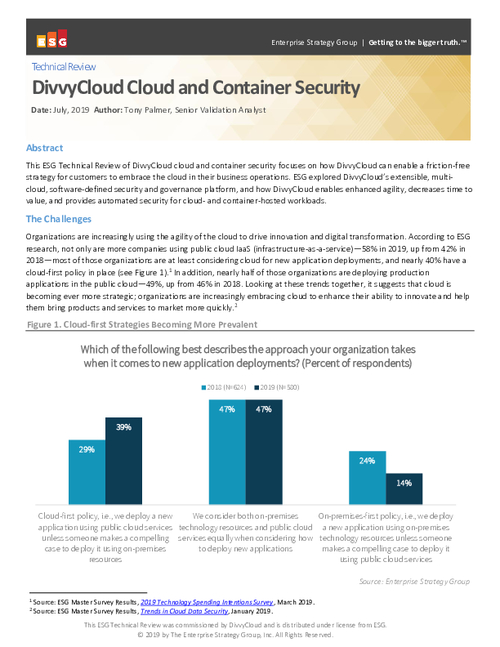
Sponsored by DivvyCloud
DivvyCloud Cloud and Container Security
Sponsored by LastPass