Detecting Compromised Credentials with UEBA
All of the biggest data breaches, judged either by number of records breached or the importance of the data stolen, have involved attackers leveraging stolen user credentials to gain access. In fact, 70-80% of attacks don't contain malware, but rather involve compromised credentials.
Download this whitepaper to learn:
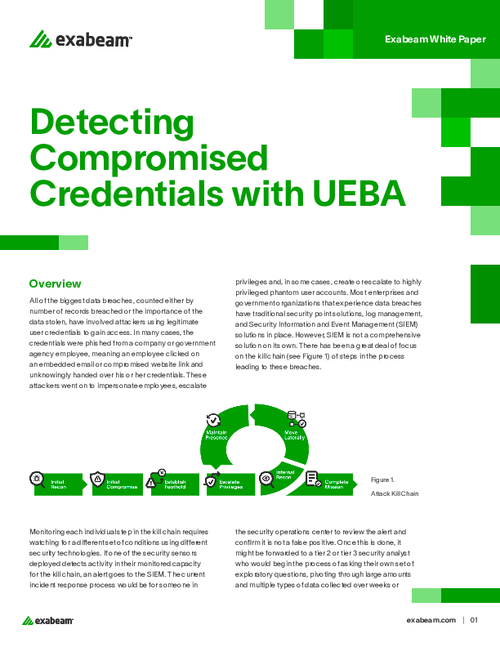
- The steps in the process leading to a breach;
- How to differentiate and separate the goals of an attacker and the goals of an employee;
- How to automate your system to detect an attacker without an overload of data.











