Sponsored by Outsystems
Sponsored by Outsystems
Doubling Your Development Speed & Efficiency with Low-Code
Sponsored by Outsystems
How to Increase App Dev Speed to Focus on Tighter Customer Data Security
Sponsored by Outsystems
How Low-Code Can Supercharge Application Development
Sponsored by Checkmarx
Automation of AST: Keeping Pace with Evolution of Software Development
Sponsored by Imperva
Global DDoS Threat Landscape
Sponsored by Synopsys
Navigating the Open Source Risk Landscape
Sponsored by WatchGuarad
Protecting New and Existing Access Point Installations from Wi-Fi Hacking
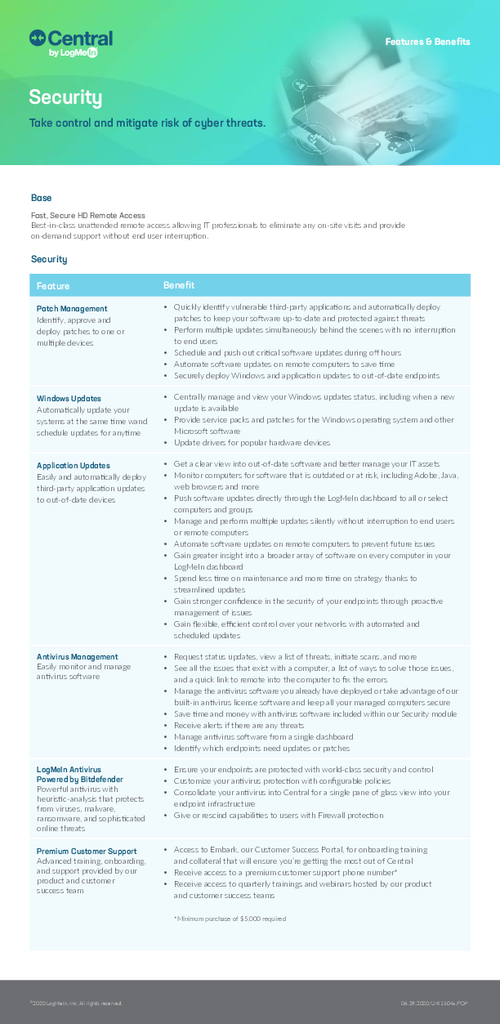
Sponsored by LogMeIn
Central Security Module Overview
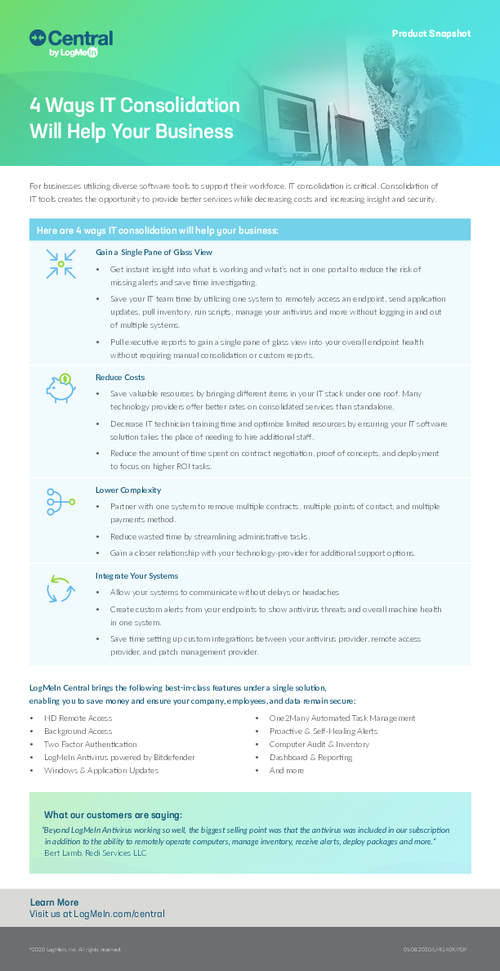
Sponsored by Central by LogMeIn
4 Ways IT Consolidation Will Help Your Business
Sponsored by Auth0
Fixing Broken Authentication
Sponsored by Security Compass