Enterprise Mobility Management / BYOD , Events , Fraud Summit
Mobile Fraud

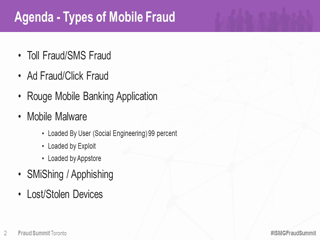
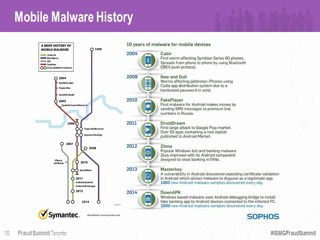
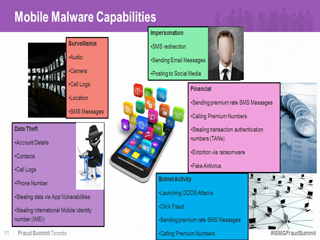
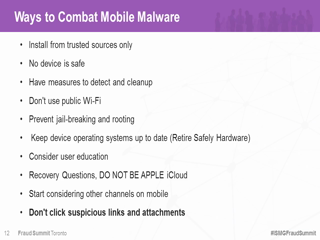
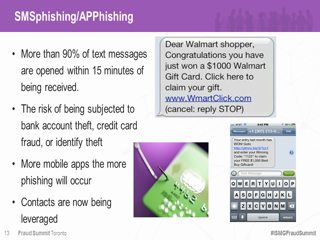
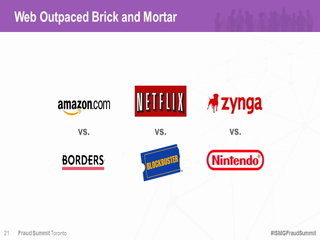
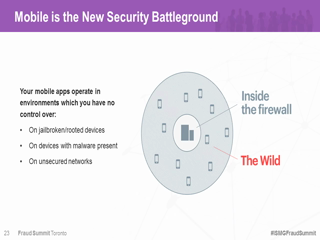
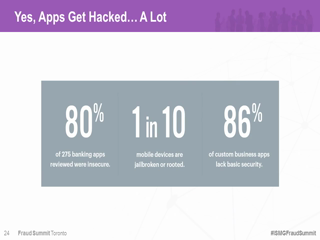
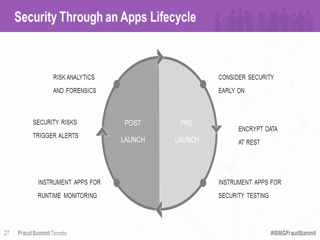
Mobile banking is growing out of its infancy and experts predict it will soon be the dominant banking and payments channel. With the vast array of endpoints being utilized, how are the threats of rogue mobile apps, mobile malware and SMiShing evolving? What are the risks inherent in mobile payments? This session reviews these emerging mobile malware threats, their impact on banking institutions and the latest technology solutions to help mitigate the risks.
See Also: A New Approach to Endpoint Security Software Testing
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.