Breach Notification , Incident & Breach Response , Managed Detection & Response (MDR)
Video Game Streamer 'Twitch' Confirms Massive Data Breach
Reports: Platform's Entire Source Code Compromised in 125GB Leak
The Amazon-owned video streaming service Twitch, which focuses on video games and e-sports broadcasts, has suffered a massive breach, which the company confirmed via Twitter on Wednesday.
See Also: A Better Way to Cover the Bases for Breach Protection
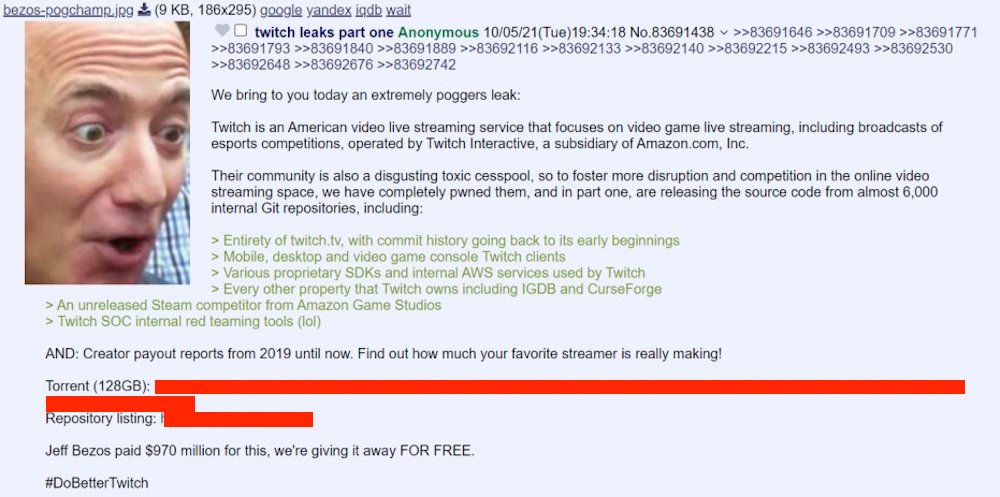
A post on the online forum 4chan indicates that about 128 GB of data was leaked, including source code and user payout information. The 4chan post says the breach was intended to "foster more disruption and competition in the online video streaming space. The post called the Twitch community a "disgusting, toxic cesspool."
Twitch tweeted on Wednesday morning: "We can confirm a breach has taken place. Our teams are working with urgency to understand the extent of this. We will update the community as soon as additional information is available. Thank you for bearing with us."
A spokesperson for Twitch tells Information Security Media Group, "Our investigation is ongoing, and we are in the process of analyzing all of the relevant logs and data to assess actual impact."
In posts to its website late Wednesday, Twitch said some data had been exposed to the internet due to an error in a Twitch server configuration change that was subsequently accessed by a malicious third party. There is no indication that either login credentials or credit card numbers have been exposed. The company said it does not store full credit card numbers. It has also reset its stream keys, which may require a manual software update.
Leaked Content
The Twitch data that the intruders claim to have stolen includes:
- Twitch's source code;
- 2019 creator payout reports, including 81 streamers earning more than $1 million;
- A compilation of Twitch clients;
- Proprietary software development kits and internal AWS services;
- Access to the Twitch-owned Internet Games Database and CurseForge;
- An unreleased Steam competitor from Amazon Game Studios;
- Twitch's internal red-teaming tools.
The leaked data also identifies and quantifies the platform's top earners. Of all of the data, this may be the most sensitive. Some popular Twitch streamers have said the figures are right, while others have said they're incorrect.
But the leak of the source code isn’t as sensitive or as bad for Twitch as some might portray it to be, says Thomas Shadwell, who founded Twitch's security team in 2014 and left in July 2020 as a senior application security engineer.
The source code is Twitch's intellectual property, he says, but it would essentially amount to instructions for reproducing Twitch. That source code poses about the same risk as any code that is open to the public, and the risk is that someone might spot an exploitable vulnerability.
Shadwell says one project he was involved with at Twitch included moving secrets such as API tokens, passwords and other items, such as test accounts, from the source code to improve overall security, Shadwell says.
The source code that was leaked likely came from one server that stored the git instance, he says. "That code is pretty much public to everyone inside Twitch," Shadwell says.
While he worked there, Twitch took steps to protect unauthorized access to the git instance, he says. For example, developers used Yubikeys, which are hardware tokens that generate time-sensitive codes for multifactor authentication. That means that an attacker who only has a login and password would be unable to access the system.
Refrring to the news about the Twitch breach, Shadwell says: "I think as a security engineer, you plan for these eventualities and you always live in a world where these things can happen."
'How on Earth?'
Those behind the leak have reportedly called it "Part One," hinting at further drops. It appears that the first wave does not include passwords, physical addresses or email addresses of Twitch subscribers, The Verge reports.
Many on social media are calling for Twitch users to activate two-factor authentication - typically requiring verification via smartphone - in their security and privacy settings, to further secure accounts.
Bill Lawrence, a former cybersecurity instructor at the U.S. Naval Academy and currently CISO with the firm SecurityGate, notes, "[Twitch's] data loss prevention and exfiltration prevention don't seem to have worked, and the volume of the hack could point to an insider or very lax controls around the keys to the 'Twitch kingdom' that an external hacker found."
Archie Agarwal, founder and CEO of ThreatModeler, says, "How on earth did someone exfiltrate 125GB of the most sensitive data imaginable without tripping a single alarm? There's going to be some very hard questions asked internally. … [And] it's almost guaranteed user information will have been swept up in this breach, and so users will have to take the usual precautions."
Recent Controversy
This week's incident follows several recent headlines that found the streaming service facing user protests - labeled the #DoBetterTwitch movement - against harassment on the channel. The topic of interest - "hate raids" - involves viewers being rerouted to different channels when streamers head offline - a tool that, if abused via bots, can result in overwhelming spamlike or hateful messaging.
Responding via a Twitter thread in August, the company said: "We've seen a lot of conversation about botting, hate raids, and other forms of harassment targeting marginalized creators. You're asking us to do better, and we know we need to do more to address these issues. That includes an open and ongoing dialogue about creator safety."
Twitch also wrote that it had identified a flaw in its protective filters, for which it rolled out an update that would better detect hate speech in chat. The company said it will be launching channel-level ban evasion detection and account verification improvements by later this year. It also said it is trying "to build a safer Twitch."
This story has been updated with a statement from Twitch, along with additional details and analysis.
Executive Editor Jeremy Kirk contributed to this report.












