Application Security , Breach Notification , Cybercrime
Update: OpenSubtitles Data Breach Affects 6.7 Million Users
Breach Happened in August 2021 and Company Paid a Ransom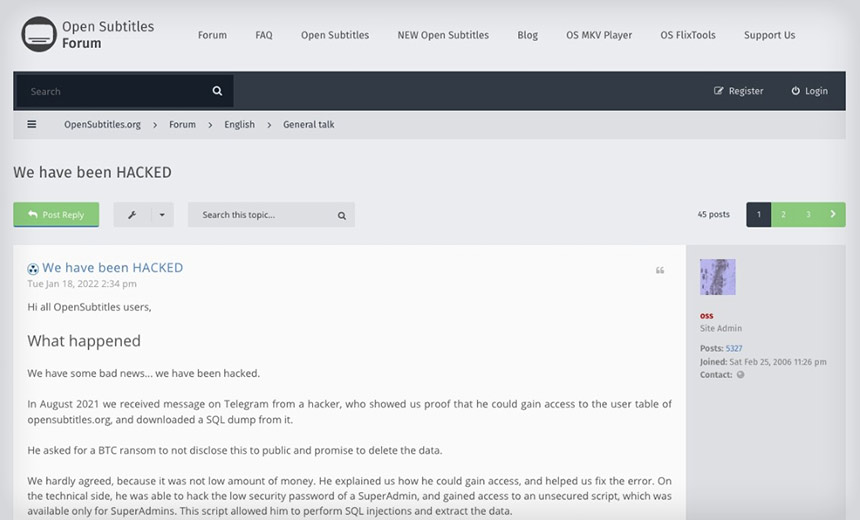
OpenSubtitles, a website providing free movie subtitles, confirmed to its users this month that it had been hacked last August and that the hacker had demanded a ransom to remain silent about the attack and to delete the leaked data. The site owner reports that he paid the ransom, but the stolen dataset has now surfaced and it appears that it could be circulating on some underground forums.
See Also: Cybersecurity for the SMB: Steps to Improve Defenses on a Smaller Scale
The OpenSubtitles data breach affects 6,783,158 users of the platform and includes personally identifiable data such as email and IP addresses, usernames, user's geolocation and passwords stored as unsalted MD5 hashes, says Troy Hunt, creator of the Have I Been Pwned data breach notification service.
New breach: Open Subtitles had almost 7M accounts breached and ransomed in Aug. Data included email and IP addresses, usernames and unsalted MD5 password hashes. 75% were already in @haveibeenpwned. Read more: https://t.co/bXCD897HRC
— Have I Been Pwned (@haveibeenpwned) January 19, 2022
What Happened
OpenSubtitles' owner tells Information Security Media Group, "To my knowledge it was 6,812,134 users - a couple of thousands of them were imported and never logged in." He says he learned about the breach through a Telegram message sent by the hacker. On a forum on the site, the owner says the hacker provided a proof of concept demonstration to the website owner to gain his trust. "[The hacker] showed us proof that he could gain access to the user table of Opensubtitles[.]org, and downloaded an SQL dump from it," the forum post says.
After contacting the owner, the hacker asked for a ransom, to be paid in bitcoins, in exchange for not disclosing the attack or subsequently leaking details of the platform's subscribers. "I paid it in parts. I don't want to disclose the amount, but it was a lot for me," the owner tells ISMG, adding that the attacker had promised to delete the data.
Hunt tells ISMG that this was not a ransomware attack in which data was encrypted and a ransom was demanded in exchange. Instead, he says, it was a genuine old-school ransom demand made in exchange for deleting the data that was leaked through the OpenSubtitles SQL database.
Initially, OpenSubtitles' owner said he was apprehensive about paying the ransom, but he gave in when the hacker promised to help secure the website - which he did. "He explained how he could gain access and helped fix the error." The owner tells ISMG how the attacker was able to hack the low security password of a SuperAdmin using a brute force attack and gained access to an unsecured script that was available only for SuperAdmins. This script allowed him to perform SQL injections and extract the data.
The owner tells ISMG that he believed he had a "gentleman's agreement" with the hacker that the data would not be revealed, given that the hacker had been helpful in securing the website and "seemed trustworthy." Unfortunately, after having paid the initial ransom, two weeks ago, the attacker's friend - believed to be the attacker - contacted the owner wanting more money. The owner refused to pay again, and "it went to today's situation," he says. He tells ISMG: "I believe the hacker sent it [the database] directly to Mr. Troy Hunt. I don't have any knowledge that the data is available on hacker forums or similar. I would also like to know."
A red-alert warning to users was put on the website home page, on unsuccessful login and on its forum prior to notification by Troy Hunt, the owner tells ISMG.
OpenSubtitles said that, "Most users didn't use strong passwords; it means hackers can get access to user accounts." The passwords of user accounts that OpenSubtitles stores at the backend were unsalted MD5 hashes, which could be another reason why the owner paid the ransom.
The owner says the site didn't use salted MD5 passwords because he had "little knowledge of security" when the website was created in 2006. Customers whose data was leaked were advised on the site: "If you used a strong password - let's say at least 8 characters with lowercase, uppercase, number and special characters - you should be safe. But short easy passwords, especially if they are [found] in the English dictionary, can rather easily be extracted from this data."
The website owner says he has accepted his mistake and learned his lesson the hard way. "We should have spent more energy on securing the site and kick out the old MD5() without salted passwords long time ago," the forum post says.
According to the website owner, the hacker did not gain access to any credit card data details as "these are stored outside of our platform."
The owner tells ISMG that despite its widespread usage, OpenSubtitles is "basically a one-man show - me, so I am doing everything. I did some stuff wrong. I think the lesson is learned and I'm trying to do my best."
Measures Taken
OpenSubtitles says that its website is more secure now and that it has taken the following security measures in response to the August 2021 data breach incident:
- The accounts will be locked after a limited number of unsuccessful logins.
- New password policies have been adopted.
- Session information has been removed from the back-end database table.
- IP addresses have been spoof-proofed.
- Captchas have been introduced on login, register and password reset pages;
- Forms will protect against cross-site request forgery.
- Requests will be canceled if admins change their IP during the session.
- All MD5() passwords have n been deleted, and user passwords are being saved using hash_hmac and SHA256 algorithm with salt and pepper.
OpenSubtitles also has asked all users to conduct a mandatory password reset so that all user passwords can be stored with the latest security changes.
Hiding the Breach?
Trevor Morgan, product manager at Comforte AG, tells ISMG that OpenSubtitles should not have kept the hack and data exposure a secret for so long. "Organizations have both a legal and an ethical responsibility to keep authorities and individuals aware of any compromising situations involving peoples' sensitive information. This consideration gives individuals the ability to change passwords and monitor all of their other accounts accordingly. Depriving them of this right is indefensible no matter how you look at it and no matter where you point fingers," he says.
Morgan also says that the entire scenario was miscalculated by OpenSubtitles' owner. "Their protocol up to this point - according to reports and their own messaging on their site forum - has been to keep a tight lid on the situation, pay the ransom, and hope that the threat actor assisted in making the situation go away. Not surprisingly, that measure didn't pay off, and account information found its way onto Have l Been Pwned. This miscalculation might have severe repercussions for users whose account information may be used for further nefarious purposes."
Steven Hope, CEO and co-founder of Authlogics, agrees and says, "No one likes to admit that they have become victim to a cyberattack, but people are renowned for using the same password across multiple accounts, which puts not only the account they hold with the recently hacked company at risk but the same password could also be linked to their email or even financial accounts, putting them at a higher risk."
Hope says OpenSubtitles was correct in informing users of what had been breached and forcing a password reset for all, but its actions came too late. "The damage is done before anyone was made aware of it," he says. "Companies need to abide by regulatory body compliance for data protection ... and customers have the right to know their data has been breached."
As the site provides services into the EU, it is required to have an EU representative and to report this breach to its lead supervisory authority and to the ICO in the U.K. within 72 hours of detecting it, Alan Calder, CEO of GRC International Group, tells ISMG. He says OpenSubtitles is in breach of both U.K. and EU GDPR.
Calder points to the website owner's statement: "Of course this is not an excuse, but there's more and more hackers, getting more and more creative and greedy, just as active against big businesses as small ones. If companies like Microsoft, Facebook, Twitter, Nintendo or Zoom can get hacked, what are our chances as a tiny team to not end up getting attacked?" and says OpenSubtitles had a "naive view" before it was attacked.
And Aimee Bush, senior privacy consultant at Bridewell Consulting, says, "If OpenSubtitles had robust breach management processes and threat and vulnerability detection in place, the risk of this breach would have been significantly reduced or potentially even a near-miss."
She also criticizes the delayed response, telling ISMG: "OpenSubtitles should have initiated their incident management process as soon as they became aware of a breach having occurred." Then, she says, the users' data would not have been unprotected for six months, and the company could have "embedded additional technical and organizational measures to prevent something of this gravity occurring again."




















