Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
Russian Gang Netted $3M Daily via Video Ad Fraud
Report: Advanced Botnet Mimics Human Behavior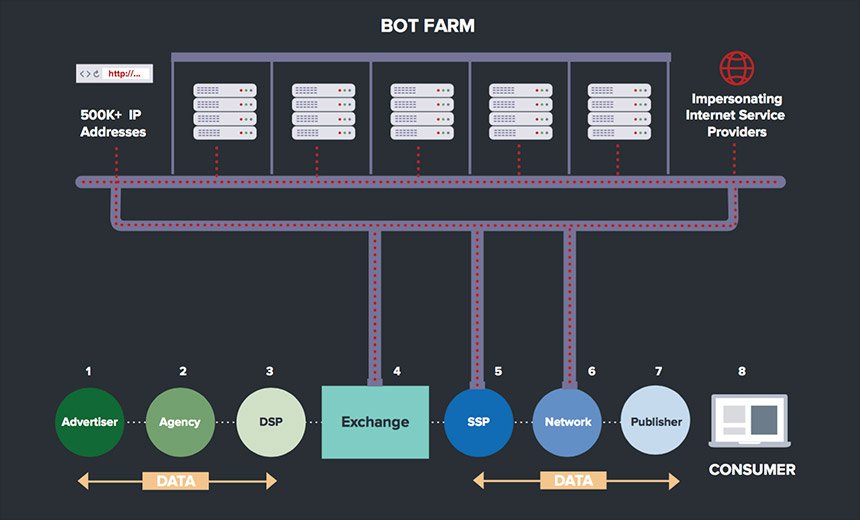
An expansive botnet run by a Russian cybercriminal gang netted more than $3 million a day by generating fake views of online video advertisements. The finding is already reinforcing concerns over the prevalence of fraud in online marketing.
See Also: Key Security Challenges and Tooling Approaches for APAC in 2024
The operation, which had been noticed by others in the industry, came to broad public attention through the release of a detailed report by White Ops, a security company that focuses on detecting fraudulent ad traffic.
White Ops says that the botnet, which it nicknamed Methbot, is "the largest and most profitable ad fraud operation to strike digital advertising to date." As many as 300 million video ads per day were viewed not by humans but by automated "bots" designed to mimic the behavior of real users online.
The victims are marketers who spent money to place video advertisements on top-tier publishers. Their ads ended up on fake websites that were designed to look like those of real publishers. White Ops estimates more than 6,000 publishers were spoofed, showing the scale of Methbot.
Video ads command some of the highest premiums in online advertising, trumping the take from text or display ads. Publishers may receive as much as $36 per 1,000 views - a metric referred to as CPM - for a video ad, although the average take is slightly more than $13, according to a report from White Ops.
Most of the techniques used by the Russian gang to game systems have been around for a long time, says Jerome Segura, a lead malware intelligence analyst with Malwarebytes. But the scale of Methbot, which employed rented infrastructure in the United States and the Netherlands rather than hacking into personal computers, is impressive, he says.
"Most of the ad fraud that you see typically is malware-based - computers that are infected," he says. "In this case, they had to buy all of this infrastructure. That costs a lot of money. It's not everybody who can do that. It's somebody who has the skills to pull this off."
Fake Surfers, Fake Sites
Digital advertising offers marketers fine-grained control over who sees their ads. The innovation has driven the growth of the industry, which is expected this year to surpass TV ad revenues, according to market researcher eMarketer.
But major players in the industry have long realized the threat cybercriminals pose to their businesses. They've also sought to tamp down doubts that digital ads may be not reaching their target audiences by employing security techniques designed to distinguish between real people and bots and by only counting impressions - times the ads were delivered to an end user - from the former.
Methbot used a variety of methods to defeat those measures and get the maximum value from each video impression. The gang used a network of more than 570,000 IP addresses to build a fraudulent network of bogus web surfers who appeared to be an attractive pool of consumers to advertisers. Those fake consumers then visited fake websites created by the gang, cheating advertisers out of their money.
The web browsers that viewed ads were rigged to have sought-after browsing histories - a metric that is used to target ads. The IP addresses were manipulated to appear to come from consumers from U.S. ISPs such as Verizon and Comcast.
The bots also came with social media credentials: Methbot forged login information that made it "appear as if a user is logged in when an impression occurs," the report says. Because bots can sometimes be detected through mechanical cursor or mouse movements, Methbot also forged that activity.
Industry Responds
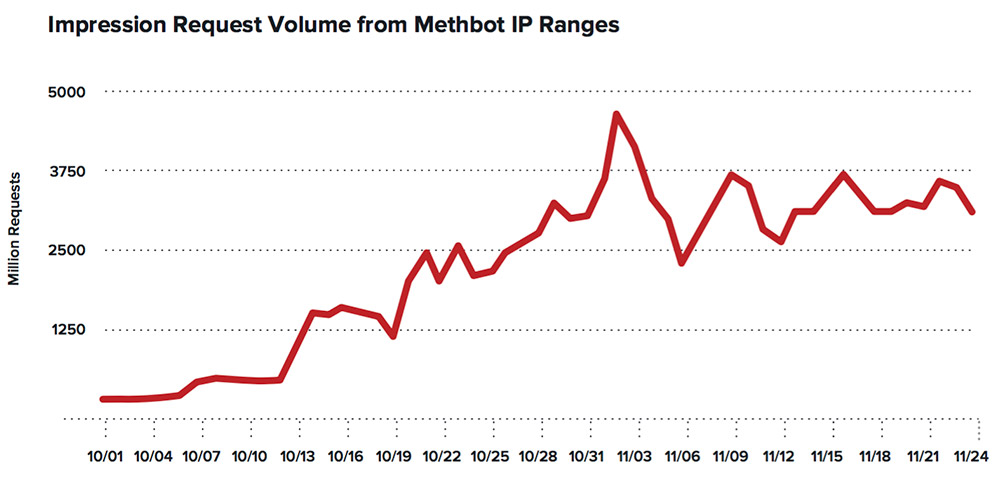
White Ops says it first identified Methbot in September 2015 after it detected a stream of bot-related traffic with a unique signature. The company noticed the traffic was affecting some of its clients. But the activity suddenly surged in October, which contributed to its recent decision to release related information publicly.
"At this point, the Methbot operation has become so embedded in the layers of the advertising ecosystem, the only way to shut it down is to make the details public to help affected parties take action," the report says.
The online advertising industry is massive, and it's difficult to keep track of the players. Segura says that large companies have a strong interest in making sure fraudulent traffic is caught quickly. But others are less motivated because they get paid whether the traffic is genuine or not. Employing security measures cuts into the bottom line.
"Not everyone has an interest in fighting fraud," Segura says. "The losers are actually their customers, their brands. Those people trust the ad industry."
Battling Methbot
White Ops' report caused a stir. One major advertising network, AppNexus, says it had caught and blocked most invalid traffic that had come from Methbot. AppNexus says that in the past week, only $500 went to IP addresses controlled by Methbot.
"Based on an initial analysis, we have a high degree of confidence that AppNexus has very limited exposure to Methbot," according to a Dec. 20 email sent by the advertising network to its customers, a copy of which was obtained by Information Security Media Group. "We continue to invest heavily to ensure that all traffic on the AppNexus platform is valid."
The ongoing gaming of online advertising has "somewhat been an elephant in the room" for a while, says Craig Spiezle, executive director and president of the nonprofit Online Trust Alliance, which offers guidance to businesses to help them battle ad fraud (see Online Ad Industry Threatened by Security Issues).
Methbot, however, will intensify questions about whether advertisers have been placing excessive numbers of digital ads on questionable publisher websites with fake news stories, Spiezle says. The traffic boost that fake news stories have received on social media sites such as Facebook and Twitter in recent months is believed to have been a powerful force in the U.S. presidential election.
"The online advertising industry is being hit with the perfect storm," Spiezle says.