Encryption & Key Management , Forensics , Security Operations
Researcher Finds New Vulnerabilities in Cellebrite's Tools
Matt Bergin of KoreLogic Says Forensic Tools Need Regular Security Audits
Can courts trust evidence collected by Cellebrite's mobile device forensic tools?
See Also: Encryption is Worthless Without Protecting Your Keys
The question was posed late last month by Signal, the messaging app that is a recent new target for Cellebrite's data-collecting tools for law enforcement. Signal's founder, Moxie Marlinspike, contended that software vulnerabilities found in Cellebrite's tools could be used to tamper with evidence. As a result, one lawyer has already filed a motion for a new trial. (see: Signal Founder Says Cellebrite's Forensics Tools Flawed).
But Marlinspike isn't the only one who has taken a close look at Cellebrite's devices. On Friday, Matt Bergin of KoreLogic will present his latest findings - which relate to Cellebrite's Universal Forensic Extraction Device, or UFED - at the Black Hat Asia conference.
Bergin, a senior information security researcher with KoreLogic, says he found three vulnerabilities in UFED. Although those issues have now been patched by Cellebrite, Bergin contends forensics software should be put through rigorous penetration testing to ferret out vulnerabilities that could jeopardize evidence.
Bergin will also demo an Android application he developed called Lock Up, which can factory reset a phone if it detects Cellebrite's software attempting to copy data. All of his research comes from a concern that Cellebrite's forensic devices could be manipulated by bad actors and potentially implicate innocent people.
"My whole goal for this project was to really highlight the fact that forensics tools are not immune to software vulnerabilities," Bergin says. "And those issues, when exploited, do have real-life implications for people. That could be the rest of your life in jail."
Cellebrite officials did not immediately reply to a request for comment.
Examining the UFED
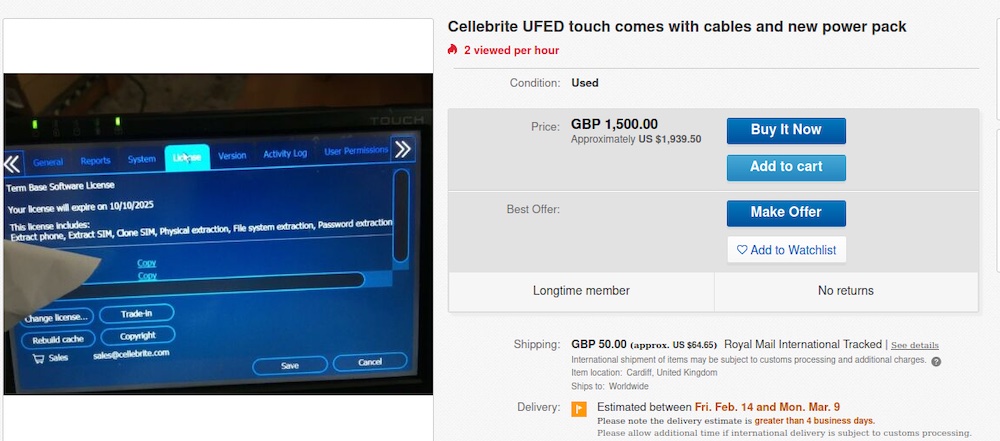
Cellebrite devices often end up on the secondhand market, on auction sites such as eBay. Some of those devices may still have valid licensing periods, meaning the devices are still getting software updates. Bergin acquired six Cellebrite UFEDs.
Because Cellebrite often uses exploits to break into devices, such as iPhones, it employs cryptography to ensure that information, which ranges from bootloaders to other specialized apps, isn't easily harvested by someone who has a UFED. Bergin, however, cracked it.
"I broke the decryption process and built my own decryptor so that I could get access to it [a UFED] regardless of their defenses," he says. "They [Cellebrite] obviously don't want their competitors to be able to easily reverse-engineer their tooling."
By breaking its cryptography, Bergin gained an inside look into how the UFED begins probing devices. That insight also allowed him to write detection signatures for how UFED interacts with a targeted device. He then created Lock Up, which is an Android app.
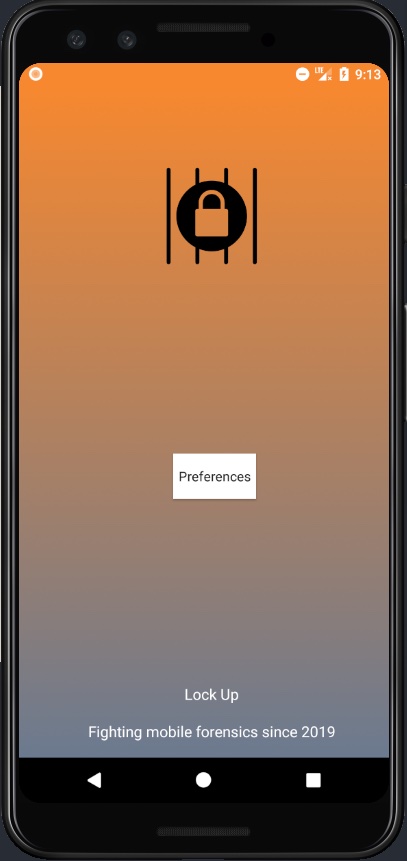
Bergin says he isn't going to publish Lock Up because he doesn't want to deliberately impede legal law enforcement investigations. But he is going to release its source code as well as the indicators of compromise, which are checksums and hashes of files that Cellebrite's UFED installs on devices prior to collecting data.
In the course of his research, Bergin also discovered three vulnerabilities, all of which Cellebrite patched. Bergin summarized his technical findings in a blog post.
Bergin found that Cellebrite's UFED versions 5.0 through 7.29 used four hard-coded and private RSA keys (CVE-2020-11723) to authenticate to the Android debug bridge daemon on targeted devices. The keys could, in theory, be used by a malicious actor to plant evidence on a mobile device while extracting data - an obvious problem that could contribute to a false accusation.
Cellebrite also fixed CVE-2020-12798, a privilege escalation vulnerability, and another problem, CVE-2020-14474, in which Cellebrite left hard-coded keys for encrypted material right next to the encrypted material.
Ways to Improve
Bergin says his findings show that forensics tools should be more thoroughly audited. There is such a program but, unfortunately, it doesn't go far enough, Bergin says.
The National Institute of Standards and Technology runs the Computer Forensics Tool Testing, or CFTT, program. It helps to ensure that if, for example, a forensics tool claims that it can extract Instagram messages, the product can actually do exactly that.
Bergin says that given the importance of the integrity of digital evidence, the program should be expanded to include penetration tests.
"We need functional testing, and we need security testing," he says. "It should be part of the CFTT process before any evidence collected by these tools can be used in a court of law."
There are also supply chain tampering concerns. Hank Leininger, co-founder of KoreLogic, says that Bergin and Marlinspike's findings have raised questions about the veracity of data. But there also could be opposite concerns, such as if Cellebrite's software was manipulated to ignore or not collect certain evidence.
Self-integrity checks could provide some assurance that software hasn't been manipulated, Leininger says. Bergin and Leininger say KoreLogic didn't find that Cellebrite ran any self-integrity checks to ensure the software hadn't been maliciously altered. The software they examined, however, is now a couple of years old, so that may have changed, they say.
Another way Cellebrite could improve its practices is by publishing prominent public notices describing vulnerabilities that have been discovered and patched. "Airing your own dirty laundry after you've washed it is a good way to build confidence in your commitment to security," Leininger says.