Cybercrime , Cybercrime as-a-service , Fraud Management & Cybercrime
PwndLocker: Free Decryptor Frees Crypto-Locked Data
Ransomware Debuted in Late 2019; Gang's Ransom Demands Have Hit $660,000 in Bitcoins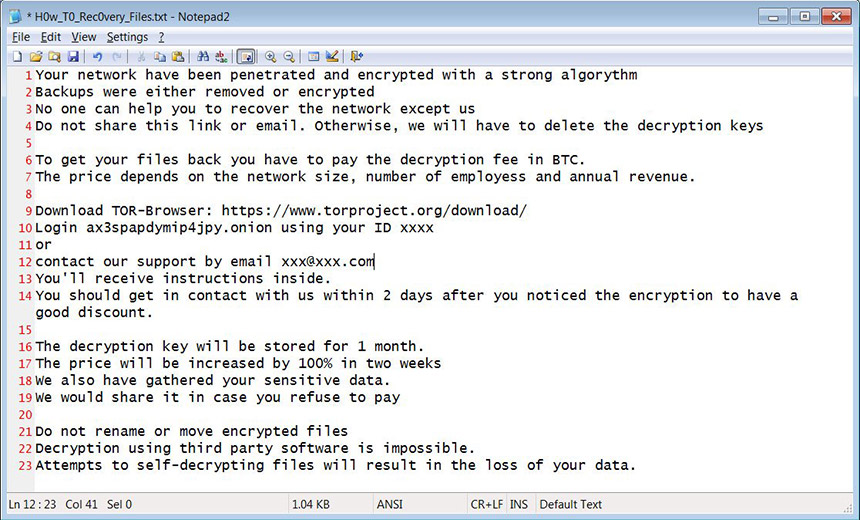
As ransomware attacks continue, law enforcement agencies and security firms are trying to help victims fight back, in part by unlocking systems that have been hit by crypto-locking malware, for free, whenever possible.
See Also: Emotet: Nastier than WannaCry and Harder to Stop
Anti-virus firm Emsisoft on Friday announced that it's developed a free decryptor for PwndLocker ransomware. That strain of crypto-locking malware has largely been targeting businesses and governments, and "has numerous variants, all of which delete shadow volume copies, limiting victims’ ability to recover," it says, with attackers then demanding $500,000 or more in exchange for the promise of a decryption tool.
The threat research group called Malware Hunter Team first publicly described the ransomware on Feb. 20.
So, there's a ransomware which we just call PwndLocker.
— MalwareHunterTeam (@malwrhunterteam) February 20, 2020
Not coded by skids...
Getting victims all over Earth...
Going for months, with like ~nothing about it public...
"The price depends on the network size, number of employess and annual revenue."@demonslay335
cc @VK_Intel pic.twitter.com/u4arK4Hn7J
Last week, Bleeping Computer reported that PwndLocker appears to have surfaced in late 2019, and said the ransomware gang claimed credit for recently hitting Lasalle County in Illinois, demanding a ransom of 50 bitcoins ($425,000), as well as the Serbian city of Novi Sad. It reports that the gang's ransom demands have ranged from $175,000 to more than $660,000.
Based on a sample of the ransomware shared by Malware Hunter Team, Bleeping Computer reports that the malware targets a number of processes and services. "Some of the applications whose services are targeted include Veeam, Microsoft SQL Server, MySQL, Exchange, Acronis, Zoolz, Backup Exec, Oracle, Internet Information Server, and security software such as Kaspersky, Malwarebytes, Sophos and McAfee," it says. "The ransomware will also target various processes and terminate them if detected. Some of the processes targeted include Firefox, Word, Excel, Access and other processes related to security software, backup applications, and database servers."
Emsisoft is one of a number of firms and organizations, including the No More Ransom project, that continue to release free decryptors, whenever possible, to help victims. These are typically made available either after security researchers or law enforcement agencies manage to obtain copies of attackers' keys, or when researchers find a way to exploit a weakness in attackers' code.
Custom Decryption Tool
Emsisoft's decryptor falls into the latter category, and also carries some caveats for success. "In order to create a custom decryption tool, we require the ransomware executable that was used in a particular attack," it says. "While the ransomware automatically deletes the executable, it is often possible to recover it using file recovery tools and it may be found in the %Temp%, C:User folders or %Appdata% folders," Emsisoft says.
Any cities or companies who are affected by #PwndLocker please contact me either here or via fw@emsisoft.com. If you know someone working on a #PwndLocker incident, please let them know how to contact me.
— Fabian Wosar (@fwosar) March 5, 2020
Emsisoft's CTO, Fabian Wosar, says he can be contacted directly by any PwndLocker victim that needs help.
How long the workaround might continue to work remains unknown. Obviously, criminals have an incentive to refine their code and eliminate flaws, so fewer victims have a way to get out for free. In the past, when researchers have found workarounds, updated ransomware fixing the weaknesses has typically arrived quickly (see: Police Push Free Decryptor for GandCrab Ransomware).
For Victims, Scattered Information
The public heads-up from Emsisoft that it may be able to help with PwndLocker infections belies a ransomware-defense problem for victims: Knowing what types of help are on offer. For some strains of ransomware, for example, free decryptors are available. For other strains of ransomware, workarounds may be available that can help victims unlock crypto-locked systems for free. But since these workarounds may exploit flaws in ransomware that security experts don't want to reveal to ransomware operators, their workarounds may not get widely widely publicized.
That's why security experts recommend ransomware victims check No More Ransom for available decryptors, as well as submit a ransom note to ID Ransomware - run by Emsisoft's Michael Gillespie - which can identify the specific strain of ransomware and provide pointers to help. In addition to those resources, ransomware incident response firm Coveware says: "If you submit a file example to us, we will have a look for free and let you know."
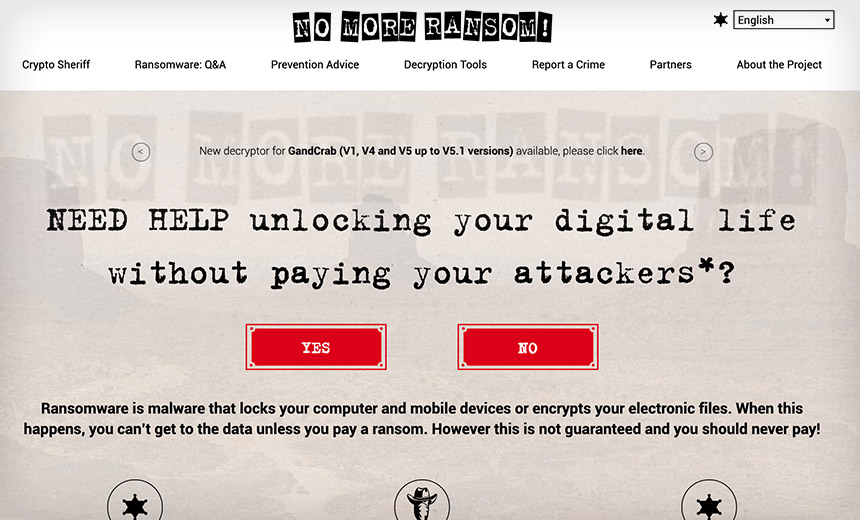
For lucky ransomware victims, such efforts may help identify at least partial "get out of jail for free" options.
Coveware emphasizes the free part of these inquiries, and cautions against paying anyone for help at this stage of a recovery effort. "You should not pay a data recovery firm or any other service provider to research your file encryption," it says. "They will use the same free resources" - as noted above - "so don’t waste your money or time."