Governance & Risk Management , HIPAA/HITECH , Incident & Breach Response
Pediatric Practice Reports Ransomware Attack
Systems Restored Quickly, But Signs of Possible Network Access
A Texas pediatric practice is the latest healthcare entity to report a major data breach following a ransomware attack, despite the organization's efforts to mitigate the incident quickly.
See Also: 9 Common Security & Compliance Risks and What You Can Do to Overcome Them
ABCD Pediatrics, in a statement, says an employee discovered "that a virus gained access and began encrypting ABCD's servers" on the morning of Feb. 6.
The practice, which operates four offices in the San Antonio area, says it received no ransom demands or other communications from the unknown attackers and that encryption "was slowed significantly" by ABCD's existing anti-malware software. ABCD immediately contacted its IT services provider, which promptly moved its servers and computers offline for analysis.
ABCD says its provider removed the virus and corrupt data from the servers. The practice said secure backup data stored separately were not compromised and used to restore data from the compromised computers.
While no confidential data, including protected health information, were lost or destroyed in the incident, exfiltration or unauthorized viewing of data could not be ruled out. "During the analysis of ABCD's servers and computers, suspicious user accounts were discovered suggesting that hackers may have accessed portions of ABCD's network," the practice says.
Exfiltration or Not?
ABCD says its IT services firm identified the malware used in the attack as Dharma Ransomware, which is a variant of an older ransomware virus called CriSiS. Although the IT firm reported to ABCD that these malware strains typically do not exfiltrate data from the server, exfiltration could not be ruled out.
"ABCD remains concerned because it discovered user logs indicating that computer programs or persons may have been on the server for a limited period of time," the practice says.
Potentially compromised data include patients' names, addresses, telephone number, date of birth, other demographic information, Social Security numbers, insurance billing information, current procedural technology codes, medical records and laboratory reports.
ABCD reported the incident to the FBI and the Department of Health and Human Services. HHS' Office for Civil Rights "wall of shame" website lists the breach as a hacking incident affecting 55,447 individuals.
ABCD did not immediately respond to an Information Security Media Group inquiry about the reported breach, including whether the unusual user log activity that was discovered during its investigation into the ransomware attack is believed to be related to that attack, or is potentially signs of a separate hacking incident.
Another Recent Attack
ABCD is at least the second Texas healthcare entity in recent weeks to report to a major breach to OCR involving ransomware, despite the organizations' apparent mitigation efforts to remove the malware and restore systems quickly with back-ups, without paying a ransom to extortionists.
Urology Austin, which operates eight offices in and around the Texas capital city, said last month that it became a victim on Jan. 22 of a ransomware attack that encrypted data stored on its servers. The breach is reported on the OCR breach reporting website as a hacking incident affecting 279,663 individuals
"Within minutes, we were alerted to the attack, our computer network was shut down, and we began an investigation," Urology Austin says in its statement. "We also began to take steps to restore the impacted data and our operations."
Lindsay Nickle, an attorney representing Urology Austin, says that mitigation effort included restoring data from backups and wiping the servers clean. During the mitigation process, patient care services were limited for only about a day as the practice restored operations. Urology Austin did not pay a ransom, she says.
Urology Austin says an internal investigation determined that patient names, addresses, dates of birth, Social Security numbers and medical information were "impacted" by the ransomware.
Although the attack did not have an impact on the practice's electronic health records, other applications, including legacy data, were potentially affected, Nickle says.
Determining a Reportable Breach
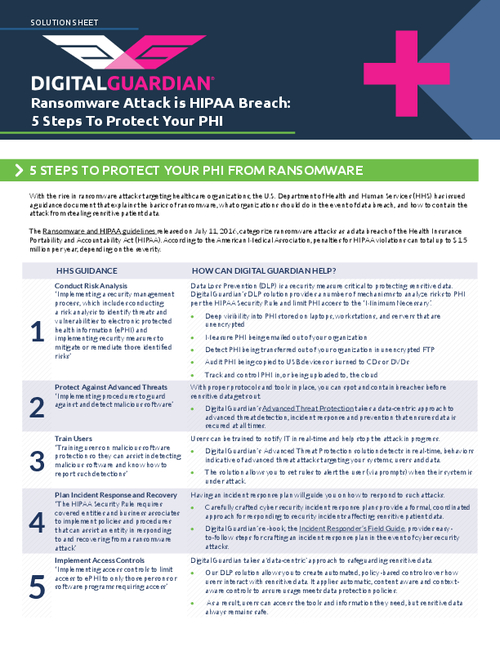
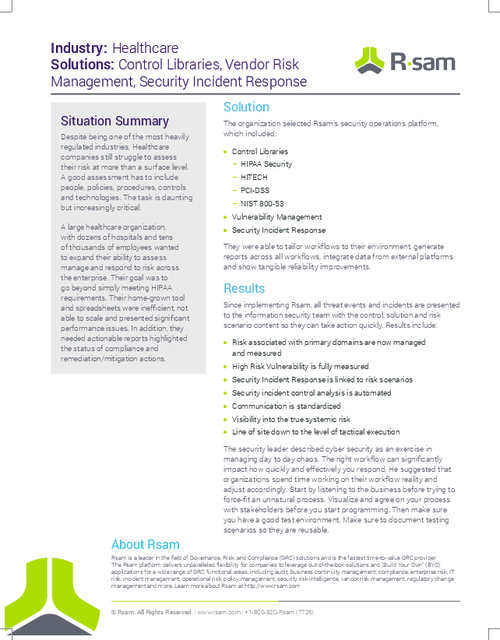
When faced with a ransomware attack, some organizations appear to have difficulty in determining whether to report the incident as a HIPAA breach to OCR.
Last July, OCR issued guidance to help covered entities and their business associates determine whether ransomware attacks are considered reportable breaches under HIPAA. The guidance notes in most cases ransomware is considered a reportable incident.
Under HIPAA , a breach is defined as the acquisition, access, use or disclosure of personal health information in a manner not permitted under the HIPAA Privacy Rule, which compromises the security or privacy of the PHI.
Kate Borten, president of privacy and security consulting firm The Marblehead Group, says ABCD made the right call in deciding to report its incident to OCR.
"HIPAA breach is a fairly low bar," Borten says. "I ask the question, 'Did your organization lose control over your PHI?' In this case, if rogue user accounts were found, maybe the accounts weren't used to access or release PHI, but it appears it was quite possible."
Taking Action
The ransomware incident at ABCD is a reminder for other healthcare entities facing the same threats. "Ransomware is still an ongoing and active problem in the healthcare industry - and obviously beyond," says privacy attorney Kirk Nahra of the law firm Wiley Rein. "It's a style of attack, which can have different root causes and different purposes. Sometimes, perpetrators are like the old Nigerian email scams - they try for lots of people just to see if something works, and may not even focus on what worked. "
To help prevent or at least detect ransomware incidents swiftly, the "best things for companies to do [is] train people on how to deal with anything that looks at all suspicious," he says. "Train staff on how to report quickly, and how to act quickly if needed. Monitor your systems carefully on an ongoing basis."
In addition, Nahra says, "look at breach notification issues carefully - HHS has given guidance on this that certainly tilts towards notification if there's no certainty on what happened."
In its statement, ABCD says it implemented various security measures before the incident, including network filtering and security monitoring, intrusion detection systems, firewalls, antivirus software, and password protection.
Following the incident, ABCD's IT services vendor located the source of the intrusion and implemented several other measures, including "state-of-the-art cyber monitoring on its network."