NIST: Over 50% Of Flaws In 2020 Were Critical or Severe
Majority of the Vulnerabilities in 2020 Did Not Require Any User Interaction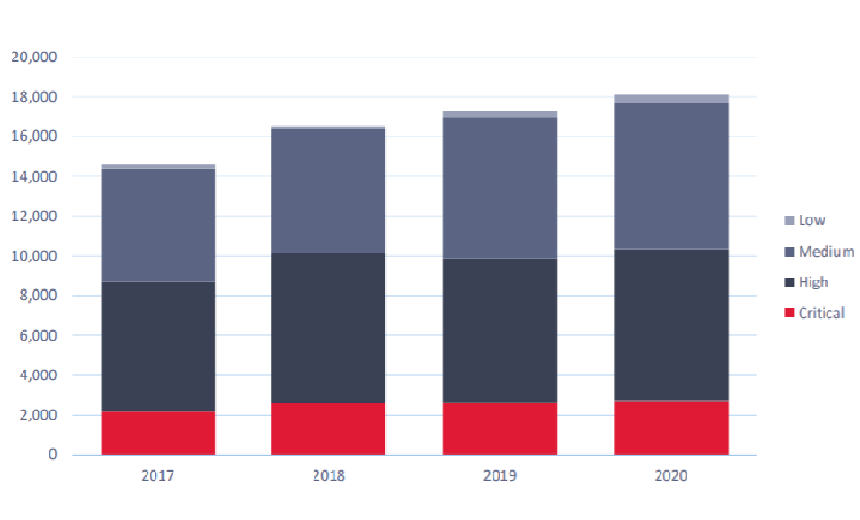
Almost two-thirds of digital security vulnerabilities recorded in 2020 were critical or highly critical and more than two thirds did not require any user interaction for exploitation, a new report by National Institute of Standard and Technology and security firm Redscan notes.
See Also: ISO/IEC 27001: The Cybersecurity Swiss Army Knife for Info Guardians
Of the 18,103 vulnerabilities that were disclosed by NIST in 2020, 57% were 'critical,' with a CVSS rating between 9.0-10.0 or 'high critical,' between 7.0-8.9 rankings.
The report also adds 68% of all the CVEs recorded in 2020 did not require any user interactions such as clicking malicious links or downloading any file for compromise. Although low-severe CVEs also increased and the report adds that attackers can chain these vulnerabilities for further compromise.
"Underestimating what appear to be low-risk vulnerabilities can leave organizations open to 'chaining' in which attackers move from one vulnerability to another to gradually gain access at increasingly critical stages," says George Glass, head of threat intelligence at Redscan. "For example, one vulnerability could provide an attacker with a low privilege shell on a host. The attacker could then move to exploit another vulnerability to allow them to become root or perform lateral movement and achieve their real objectives, whether that's installing ransomware or stealing data."
Critical Vulnerabilities
Among the severe vulnerabilities disclosed in 2020 were:
- CVE-2020-0610: A remote code execution vulnerability in Windows Remote Desktop Gateway or RD Gateway that can allow unauthenticated attackers to connect to the target system using RDP and send specially crafted requests.
- CVE-2021-21270: A vulnerability in OctopusDSC version 4.0.977, which can allow attackers to access a customer API key used to connect to Octopus Server which is exposed via logging in plaintext.
- CVE-2020-25990: A vulnerability in WebsiteBaker 2.12.2, remote access tool that enables SQL Injection that can allow attackers to compromise the application, access or modify data, or exploit latent vulnerabilities.
Common Attack Vector
The report notes the some of the common CVES that could be used as an attack vector by threat actors were found in network applications, although these vulnerabilities gradually reduced in 2020.
"The number of CVEs that can be exploited over the network is down," the report notes. "It is also important to note that these numbers may have been artificially reduced. Tech giants such as Google and Microsoft have to do a lot to maintain their products and services day-to-day. It is common for them to discover vulnerabilities that are not being exploited in the wild and release a quick patch instead of assigning a CVE. This may account for fewer CVEs with a network attack vector in recent years."
In addition, the report notes attackers can leverage vulnerabilities locally via keyboard or through flaws in USB ports. Another common attack vector depends on the proximity of the victims, where attackers can use vulnerabilities in Wi-Fi or Bluetooth devices.
Recommendation
For better vulnerability management NIST and Redscan recommend that organizations take the following steps:
- Leverage the latest open-source threat intelligence to stay informed about new and emerging threats and vulnerabilities, as well as gaining real-life context.
- Commission penetration testing to help identify hidden vulnerabilities and better understand how they might be exploited by cybercriminals.
- Monitor networks and endpoints for evidence of vulnerability exploitation.
- Conduct threat modelling exercises to obtain an overview of an attacker’s potential attack path.
- Formalize and test incident response procedures to respond quickly and effectively to breaches.
"The number of CVEs logged by NIST is rising every year, and this should serve as a reminder to organizations about the importance of keeping up with patch management," the report notes. "Critical and high priority vulnerabilities should be the focus in most instances, but it’s also important not to lose sight of some lower-level vulnerabilities that, once chained together, can also present a significant threat."













