Cybercrime , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
MuddyWater APT Group Upgrades Tactics to Avoid Detection
Researchers: New 'BlackWater' Campaign Shows Changes in Tactics, Techniques, Procedures
MuddyWater, a relatively new advanced persistent threat group that is targeting organizations in the Middle East, has changed some of its tactics to avoid detection while continuing to plant backdoors within targeted networks, according to new research from Cisco Talos.
See Also: OnDemand | API Protection – The Strategy of Protecting Your APIs
In a blog posted Monday, Cisco Talos researchers write that they have "moderate confidence" a new campaign called "BlackWater" is tied to MuddyWater. That campaign, which is mainly focused on targets in Turkey, shows that the group is changing its preferred tactics, techniques and procedures to help avoid detection and bypass certain security controls, the researchers say.
And while avoiding endpoint detection helps improve this group's overall operational security, the main goal of BlackWater is still to plant a PowerShell-based backdoor within a target's network and gain remote access, the researchers note.
"Due to the relation to MuddyWater and that actor's previous methods, we suspect the larger goal [of BlackWater] was cyberespionage," Matt Valites, threat research manager for Cisco Talos Outreach, tells Information Security Media Group.
First spotted in 2017, MuddyWater has used spear-phishing techniques to target government agencies, military institutions, telecommunications companies and universities throughout the Middle East, including Turkey, Iraq, Saudi Arabia, Jordan and Azerbaijan, according to a previous analysis by Kaspersky Lab. The group has also attempted operations in the U.S. and Europe as part of an ongoing espionage campaign, that report found.
So far, neither Kasperky nor Cisco Talos has specifically tied MuddyWater, which also goes by the name Seedworm and TEMP.Zagros, to a nation-state.
New Ways Around Security
The new BlackWater campaign starts with an obfuscated Visual Basic for Applications script, which is designed to create persistence within the target network and infiltrate vulnerable Windows systems. As with other operations, the attack starts with a phishing email that contains a malicious document, according to Cisco Talos
In an April 23 incident, the Cisco Talos researchers found that the attackers used an attached document called "company information list.doc," which contained malicious code. This code contained a macro called "BlackWater.bas," which was password-protected and inaccessible if the users attempted to view it within Visual Basic. The macro was obfuscated using a technique where characters are replaced with their corresponding integer.
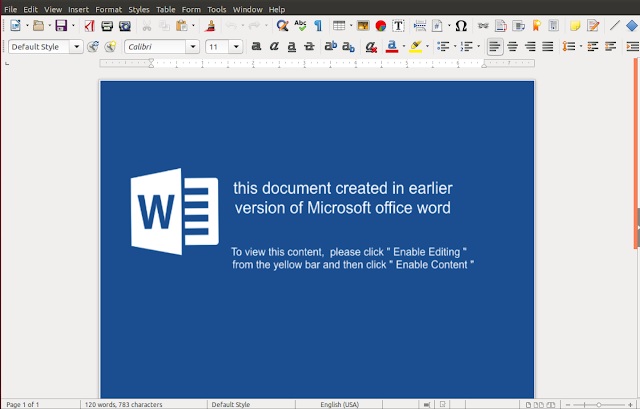
The use of this macro is one of the three new techniques MuddyWater is using in the ongoing BlackWater campaign to help obscure the operation.
The second tactic is using a PowerShell stager script, which contains its own Trojan that acts like a legitimate red-team tool used in penetration testing. This malware is controlled by the actor's server and contains an enumeration component based on the open-source FruityC2 framework that is found on GitHub. Once installed, this checks weblogs and can alert the attacks if anyone from the security team starts an investigation, researchers say.
Finally, this same payload starts to send information and data to a different command-and-control server within a URL field. This makes it much more difficult for security teams to detect data that is being transferred out of the network because it's not being written to the server and no files are created, researchers note.
While all three tactics need to be present for this particular operation to work, Valites notes that the use of the FruityC2 code to help hide some of the activity of the attackers has drawn the most interest from his research team.
"The threat actor's use of the FruityC2 component is interesting in that it's a change in tactics from previous MuddyWater activity," Valites says. "With this new FruityC2 component, the adversary no longer leaves forensic artifacts of activity on the disk, and instead exfiltrates data directly to their C2 server."
New Developments
In February and March, the Cisco Talos researchers found that MuddyWater was operating in its usual manner, attempting to install backdoors in networks using PowerShell exploits. The three new techniques started to appear in April.
The result is an additionally layer of operational security for the attackers. That's because a security team would have to go through a multistep process to determine if the network was compromised, according to Cisco Talos.
"We found a number of defense aversion tactics. For instance, by directly exfiltrating data via FruityC2, the attacker attempts to make forensic investigation more difficult by eliminating a previous disk artifact," Valites says. "Additionally, we observed additional attempts to evade detection, such as changing variables names in a supposed attempt to avoid detection by Yara."
Yara is the open-source tool used to identify and classify malware samples.
It was through MuddyWater's use of PowerShell, however, that the Cisco Talos researchers were able to tie the group to the BlackWater operation. Within the new attack, the researchers noticed a file named "crf.txt," which was also used against Kurdish organizations in Turkey that MuddyWater had previously targeted, the report notes.