Incident & Breach Response , Managed Detection & Response (MDR) , Security Operations
Insights on Revamping Recovery Strategies
Experts at Dell Technologies and Unisys Discuss Current Threats and Best Security PracticesIn a joint video interview, David Finley at Dell Technologies and Andrew Peters at Unisys offer insights on enterprise strategies for disaster recovery and cyber recovery in light of emerging threats.
See Also: Demystifying Managed Detection and Response Services
Peters and Finley discuss security issues that will be addressed in an upcoming series of Information Security Media Group virtual roundtables. Those include:
- The difference between disaster recovery and cyber recovery;
- How organizations should protect their data in case of a ransomware attack;
- What organizations don't understand about attackers' capabilities.
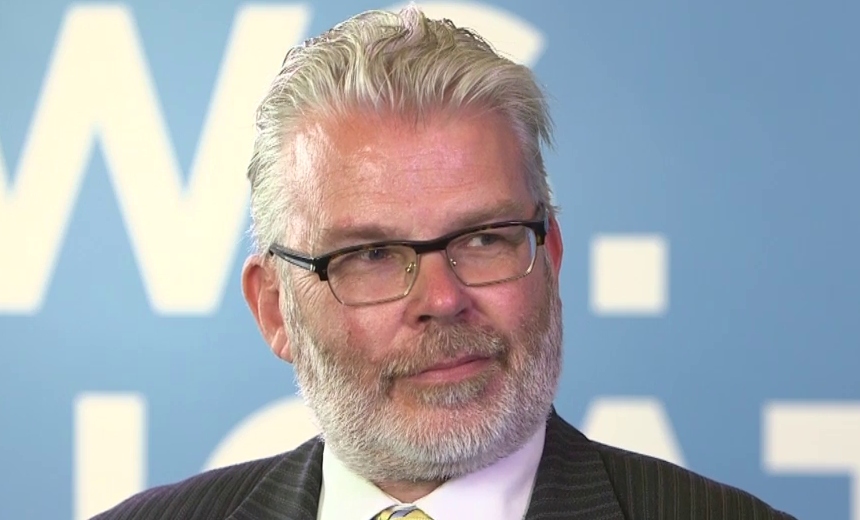
Finley is the global director of information assurance and cybersecurity for the data protection division of Dell Technologies. He has a global view of information security and a specialty in recovery after destructive cyberattacks. Finley has over 30 years of IT experience, having worked in the fields of software development, access controls, penetration testing, ethical hacking and IT management.
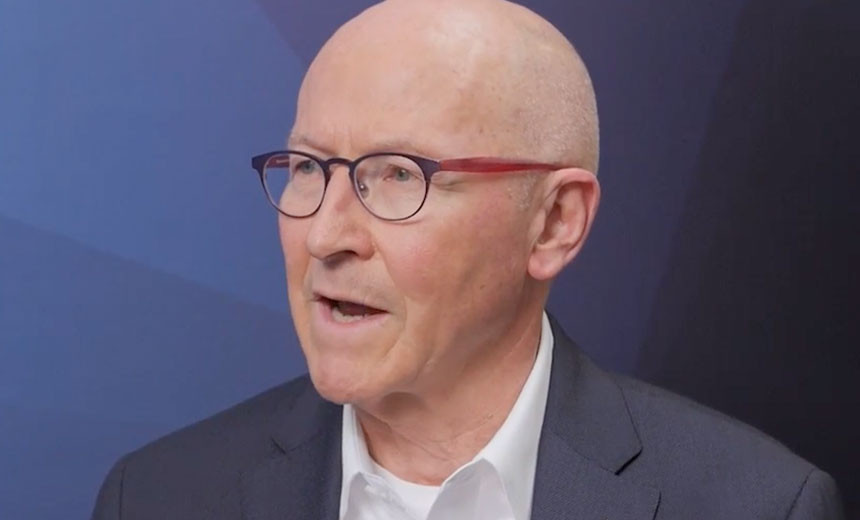
Peters, stealth industry director at Unisys, has a 25-year background in cybersecurity that includes work at the U.S. Air Force Information Warfare Center team that created the first commercial intrusion detection technology at WheelGroup, and he helped turn it into a security staple during his tenure at Cisco Systems. Andrew has experience in networking and security technologies in multiple industries and applications.