Healthcare: Fresh Target for Hackers
Community Health Systems Breach Highlights Vulnerabilities
News of another massive hacker attack in the healthcare arena offers more proof that hackers are now hitting organizations in this sector because they're perceived as easier targets than those in other sectors, information security experts say.
See Also: Financial Services, Fraud and the Future of Digital Onboarding
A hacker group from China is suspected of breaching the systems of Community Health Systems Inc., pilfering the personal information of 4.5 million patients (see: China Hackers Suspected in Health Breach). The company operates 206 hospitals in 29 states.
Compromised information includes names, addresses, birthdates, telephone numbers and Social Security numbers for patients who, in the last five years, were referred for or received services from physicians affiliated with Community Health Systems.
In another recent major health data hacking incident, the Montana Department of Public Health and Human Services confirmed a server breach impacting up to 1.3 million individuals.
"We are seeing an increase in attacks within healthcare," says Ann Patterson, senior vice president and program director of the Medical Identity Fraud Alliance. "The healthcare sector's security and privacy controls differ from more secure industries, such as financial services, and [healthcare organizations] may be easier targets."
Mandiant, which is providing forensics services to Community Health Systems, believes that an "advanced persistent threat group originating from China used highly sophisticated malware and technology to attack the company's systems," according to the hospital chain's 8-K filing to the U.S. Securities and Exchange Commission. "The company has been informed by federal authorities and Mandiant that this intruder has typically sought valuable intellectual property, such as medical device and equipment development data," the hospital chain's filing notes.
Community Health Systems declined to comment on the breach. Mandiant did not respond to a request for additional information.
Community Health Systems' Hospital Locations
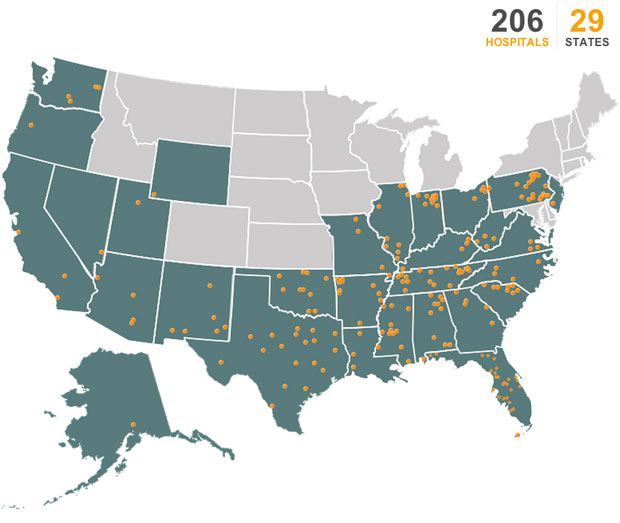
Source: Community Health Systems
Perceived Vulnerabilities
Experts say the latest attack signifies that hackers are focusing more on healthcare organizations because many have relatively weak security controls even though they store massive amounts of valuable personal information, including Social Security numbers (see: Why Hackers Are Targeting Health Data). But some observers question whether, in fact, a group from China was actually involved in the attack on Community Health Systems, because such an attack against hospitals to steal patient information is so unusual.
It's possible that the hackers were not originally going after patient data, says Tyler Shields, a security analyst at Forrester Research. "But given the opportunity to pilfer it, they chose to grab it," he says.
To mitigate the risk of hacker attacks, security experts advise healthcare organizations to conduct penetration tests and ensure they implement appropriate enterprisewide risk-based controls to protect sensitive data. The National Institute for Security and Technology's cybersecurity framework can be particularly helpful in creating a breach prevention plan, says Christopher Paidhrin, security administration manager at PeaceHealth, a healthcare delivery system in the Pacific Northwest.
More Attacks to Come
Shields contends that even if there's not continued interest from hacking groups in other countries like China, "we will certainly see continued uptake from general cybercriminals looking to compromise personal and private information that is stored in healthcare computing systems."
Dan Berger, president and CEO of Redspin, a penetration testing provider, notes: "Healthcare records are valuable on the black market. So you now have an economically viable model for hackers to invest in a dedicated effort over time."
The healthcare industry should be bracing for more large-scale hacker attacks, says Jeffrey Carr, CEO of Taia Global, a security vendor. "Identity theft is worth money if done on a large scale," he says. "Intellectual property is worth a lot of money in medical R&D."
Still, hacking incidents in healthcare have been relatively rare in recent years, according to statistics compiled by the U.S. Department of Health and Human Services' Office for Civil Rights. The OCR's "wall of shame," which lists breaches affecting 500 or more individuals, contains more than 1,080 breach incidents affecting a total of about 33.8 million individuals reported since September 2009, when the HIPAA breach notification rule took effect. Of those incidents, about 75 have hacking listed as the primary cause, and those breaches affected a total of about 3 million patients (Community Health Systems' breach is not yet on the list).
But OCR's breach list is not necessarily an accurate measure of hacking activity in healthcare, says Mac McMillan, CEO of security consulting firm CynergisTek. "I don't believe that the number of hacking events represented on that list is reflective of reality, primarily because we still have very little proactive monitoring in healthcare and many organizations with immature control environments."
China Connection
The hospital chain's announcement that an advanced persistent threat group originating from China is suspected in its breach has raised some eyebrows among security experts.
Shields of Forrester says healthcare incidents involving Chinese hackers are unusual. "I have not heard of direct healthcare attacks before," he says. "I have heard of industrial espionage-type attacks where they target the manufacturer of medical devices and equipment, but not the end-point hospitals."
But Berger at Redspin contends there have been some earlier attacks where Chinese hackers targeted healthcare organizations for their research.
Plus, McMillan of CynergisTek notes that a few years ago, his company "had a client who was hit by a particularly aggressive malware that not only compromised several systems, disabled certain security features, created temporary files and moved sensitive information into those files, but also had a command-and-control payload that was meant to send those files out to an address in China."
Forensic investigators often make judgment calls on who's responsible for an attack based on technical indicators, Carr at Taia Global notes. "[But] until an arrest is made, no one really knows who's responsible," he says.
Mitigating the Risks
To mitigate the risks of hacker attacks, organizations need to ensure their HIPAA security risk analysis process includes the identification of threats and vulnerabilities through technical security testing, Berger says. "In our opinion, that is an essential part of a risk analysis," he explains. "Also, we recommend advanced penetration testing to our larger healthcare clients, precisely to identify the likely paths that a malicious attacker may take before there is a breach."
Patterson at the Medical Identity Fraud Alliance says organizations should implement appropriate enterprisewide risk-based controls to protect sensitive information. That includes protections for electronic health records as well as mobile devices "and protection of data at rest and in transit" through encryption, she says.
It's essential for healthcare organizations to ramp up breach prevention and detection, says security expert Brian Evans, senior managing consultant with IBM Security Services.
"Deterrence, prevention, detection and response all have their place," Evans says. Prevention is preferable to detection and reaction. But without data collection, an organization cannot successfully detect or react to anything, Evans says. "Alarms, audit and investigation all require underlying information to detect bad actors and to determine the effectiveness of controls."