Account Takeover Fraud , Cybercrime , Fraud Management & Cybercrime
Hackers Use Mobile Emulators to Steal Millions
IBM: Attackers Target Mobile Banking Customers in US, Europe
IBM Trusteer reports that a hacking group is using mobile emulators to spoof banking customers' mobile devices and steal millions of dollars from banks in the U.S. and Europe.
See Also: OnDemand Webinar | For Retail : Preventing Application Fraud while Removing User Friction
Although the first wave of attacks using these mobile emulators has been stopped and the banks affected by the hacking have been notified, a second wave of attempts is likely already underway, says Limor Kessem, executive security adviser with IBM Security.
Mobile emulators, which can mimic the activities of mobile devices, typically are used by developers to test applications and features on a wide array of device types.
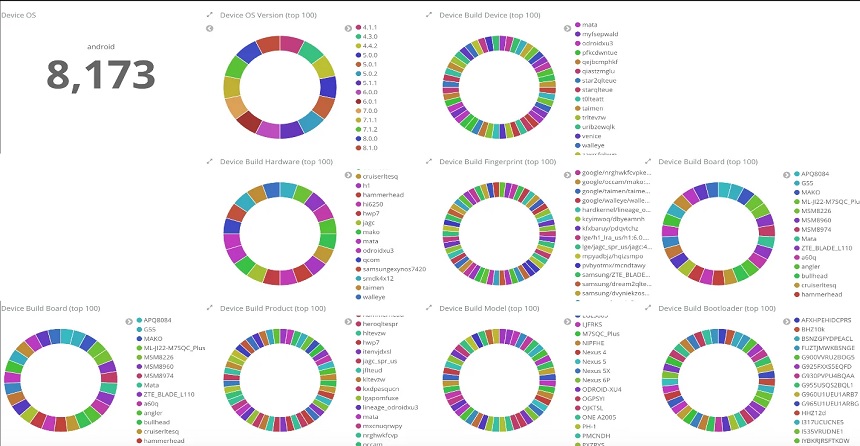
In the case IBM examined, the attackers used 20 mobile emulators to spoof over 16,000 compromised devices.
"The attackers use these emulators to repeatedly access thousands of customer accounts and ended up stealing millions of dollars in a matter of just a few days in each case,” according to an IBM report. “After one spree, the attackers shut down the operation, wiped traces and prepared for the next attack.”
Step by Step
Once attackers compromised a targeted device – using phishing emails or delivering malware in another way - they collected information, such as the victim's bank account usernames and passwords, device identifiers and SMS messages, Kessem says.
The attackers added this information to a database that was fed into mobile emulators, which then began spoofing the legitimate devices, according to IBM. Some of the details used to imitate a device included the version of the operating system used by the device and the International Mobile Equipment Identity number, which is unique to each mobile phone.
From there, the attackers could then enter bank account credentials into apps and start producing fake money orders or use other means to drain accounts, according to the report. Hackers monitored the progress of each attack, making adjustments and terminating a transaction if they discerned a bank had likely detected the attack.
"This mobile fraud operation managed to automate the process of accessing accounts, initiating a transaction, receiving and stealing a second factor - SMS in this case - and in many cases using those codes to complete illicit transactions," according to IBM. "The data sources, scripts and customized applications the gang created flowed in one automated process, which provided speed that allowed them to rob millions of dollars from each victimized bank within a matter of days."
To bypass the security features banks use to protect customers, the emulators spoofed the GPS location. They then connected to the account through a matching VPN service, according to the report. The attackers also could bypass protections, such as multifactor authentication, because they already had access to the victims' SMS messages.
"A key takeaway here is that mobile malware has graduated to a fully automated process that should raise concern across the global financial services sector,” Kesem says. “We have never seen a comparable operation in the past, and the same gang is likely bound to repeat these attacks. But they are also already being offered 'as-a-service' via underground venues to other cybercriminals. We also suspect that these scaled, sporadic attacks are going to become a more common way cybercriminals target banks and their customers through the mobile banking channel in 2021."
Role of Emulators
The IBM report notes that each time an emulator successfully spoofed a device and used it to compromise an account, the spoofed device was then discarded and replaced by another spoofed device and the cycle of attack started over. In some cases, the attackers made it appear to the bank that the customer was attempting to access an account from a new device, which helped further trick security protections.
IBM's researchers found that one emulator was able to spoof over 8,000 devices in a short time. Kessem notes obtaining access to mobile emulators is easy and inexpensive.
Although it's not clear who the attackers are, they appear well-funded and technically savvy, Kessem says.
"These uncovered emulator farms are highly sophisticated, allowing for scaled attacks and the testing and tweaking of fraud mechanisms," says Eugene Kolodenker, staff security intelligence engineer at Lookout, which specializes in mobile security. "By using emulators, the threat actor is able to move the fraud performing actions off of the infected device to a more maliciously controlled environment."