Cybercrime , Cyberwarfare / Nation-State Attacks , Forensics
Exclusive: Hackers Hit Virgin Mobile in Saudi Arabia
Attackers Offered Active Directory, Email Data on Dark Web
Hackers compromised Virgin Mobile’s office network in Saudi Arabia, gained access to its email system and an Active Directory domain controller and offered stolen data for sale on private dark web forums.
See Also: The State of Organizations' Security Posture as of Q1 2018
Security researchers who acquired the stolen data warned Virgin Mobile KSA (Kingdom of Saudi Arabia), which secured its network Friday, according to a source with knowledge of the attack. Virgin Mobile KSA is a locally owned franchise of the brand, which is owned by Virgin Group.
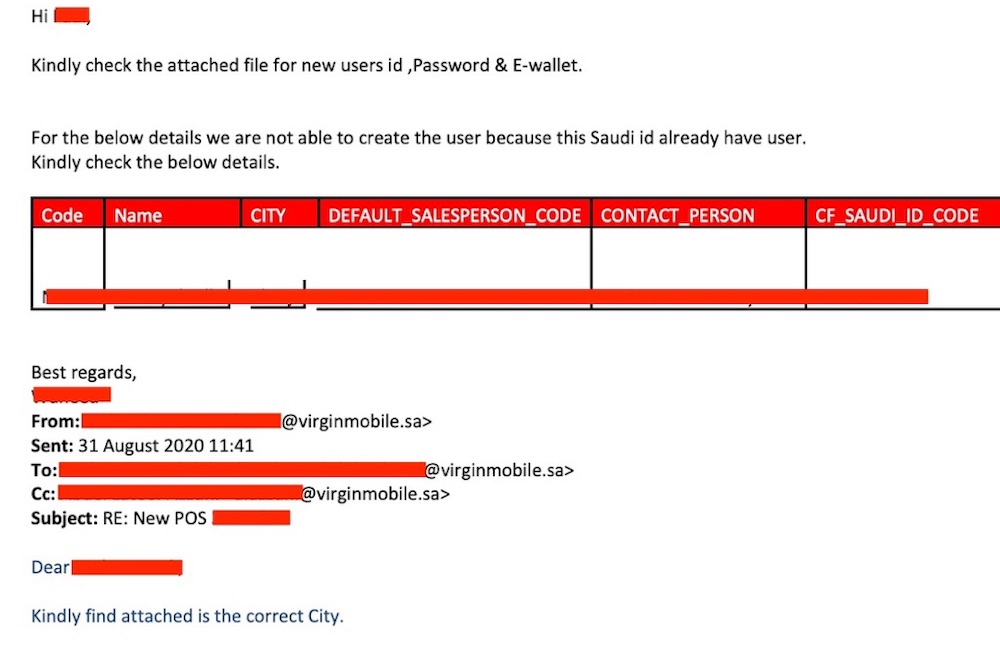
Leaked data includes recent emails Virgin Mobile KSA employees sent to each other, reports on new customer activations, dealer login activity and spreadsheets on the performance of account managers. It also includes a list of more than 1,000 accounts with usernames, employee names, email addresses and logs of when those employees last changed their passwords, among other details.
A Virgin Mobile KSA spokesperson told Information Security Media Group on Saturday that the incident has been remediated and that no customer data was breached. The spokesperson says the intrusion occurred due to “a Microsoft Exchange-related issue, which was recently addressed by Microsoft with a patch. We have taken extensive measures to protect our systems and continue to probe our security infrastructure to ensure that there are no further vulnerabilities."
Virgin Mobile did not answer follow-up questions about the attack, such as how long the intruders were in its systems or the specific CVE number of the vulnerability. Timestamps of the stolen data, however, show it was taken from the company’s network on July 7, so the intrusion may have persisted for at least two months.
ISMG showed samples of the data that the hackers took from the company’s network to outside computer security experts not involved in the investigation to garner their input. Troy Hunt, a data breach expert who runs the free Have I Been Pwned data breach notification service, says the samples appear “highly credible."
Hunt says: "There are multiple data attributes which wouldn’t normally be accessible by parties outside their private network. You need a bunch of different things to go wrong in order to get to where they [the attackers] got to."
Telecoms: Hot Target
The attack against Virgin Mobile KSA is just one of a number of cybersecurity incidents to have affected organizations in the Middle East over the past few weeks. Targets have included energy companies, governments, technology companies and financial service companies in such countries as Saudi Arabia, Israel, Jordan, the United Arab Emirates and Qatar, the source says, adding that investigators suspect that the same group is behind all of those attacks.
Telecommunication companies are of high interest to attackers. Interlopers on telecom networks could potentially identify the location of specific mobile users, steal personal information and call records and even potentially engage in more technically sophisticated tricks, such as rerouting SMS messages.
But the Virgin Mobile KSA intrusion may just be confined to its office network. The company is a mobile virtual network operator and uses the call network infrastructure of Saudi Telecom Company. STC provides operational equipment for call routing and messaging, and the stolen data solely relates to Virgin Mobile KSA, not STC.
Last year, the Israeli firm Cybereason revealed research into a Chinese group suspected of compromising at least 10 global telecommunications companies. The group’s aim appeared to be to collect call detail records for certain individuals, and the attackers also targeted organizations’ Active Directory installations (see Chinese Hackers Play Operator With Global Telcos).
Analysts say online attackers regularly try to sell stolen corporate network credentials and data on cybercrime forums. Some attackers sell working credentials or stolen data because they've finished using them or because they were able to collect them while hacking into a network for other purposes.
With Virgin Mobile KSA, it's possible the attackers are trying to make some money on the side after they’ve accomplished their primary goal, says Gene Yoo, CEO of Resecurity, a Los Angeles-based threat intelligence company. Ohad Zaidenberg, the lead cyber intelligence researcher with ClearSky, a U.K. based threat intelligence company, says he’s seen at least two hacking groups sell data on the side.
The source with knowledge of the Virgin Mobile KSA attacks says the attackers weren’t asking for a specific price for the data but rather testing the waters to see how much someone might pay for it.
One Australian security expert, who asked not to be identified, reviewed a list of IP addresses linked to the attack against Virgin Mobile KSA and said one IP address has previously been linked with activity attributed to the hacking group APT35, also known as "Cobalt Gypsy" or "Charming Kitten." Security experts suspect that group is linked with Iran but caution that online attacks cannot and should not be attributed based on a single IP address, not least when it comes to apparent Iranian hacking campaigns.
Target: Active Directory
Post-breach, digital forensic investigators often struggle to identify exactly how intruders gained access to a network, especially if the breached organization lacks robust monitoring or attackers successfully hide their attacks. But the source with knowledge of the Virgin Mobile attack notes that many recent attacks have targeted CVE-2020-0688, a serious vulnerability in Microsoft Exchange, for which a patch was released on Feb. 11.
It’s possible that Virgin Mobile KSA delayed patching CVE-2020-0688 but ended up getting stung by it. Jake Williams, a former network exploitation engineer with the NSA who now runs Rendition Infosec, says scheduling downtime “to patch a system results in immediate productivity loss, but the benefit of doing so is less clear (and never immediate).”
“Just like it's hard to say, ‘That one time I went to the doctor to get labs drawn was the time that saved me from a heart attack,’ it's hard to say which patch will prevent a breach,” Williams says.
An overview of the flaw published by Trend Micro’s Zero Day Initiative in February notes that the vulnerability stems from Exchange “failing to properly create unique cryptographic keys at the time of installation" and affected all versions of Exchange up to that point.
In the Virgin Mobile KSA attack, after hackers were inside the network, they compromised an Active Directory domain controller, the source says. Active Directory is Microsoft’s software for managing user authentication and access to network resources, and it could be used to completely compromise any account or obtain virtually any data inside the organization (see: Why Hackers Abuse Active Directory). The attackers then used an open source research tool called ADRecon to exfiltrate all of the data from Active Directory.
At Virgin Mobile KSA, the hacked domain controller is linked to 387 hosts, which range from Windows 10 Pro machines and Windows 7 systems to boxes running Windows Server 2008 and Server 2012, the source says. Most of the hosts appear to be related to computers used by Virgin Mobile KSA office employees, the source adds.
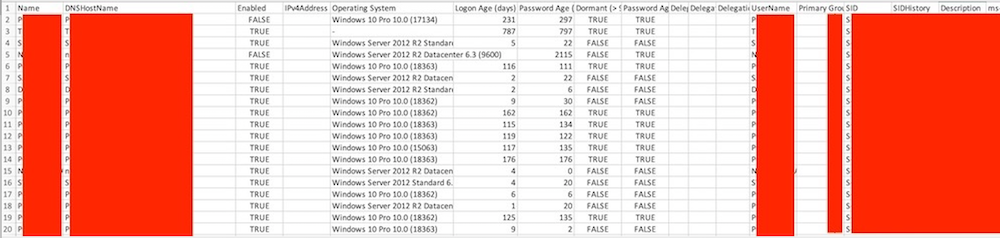
The attackers also obtained the NTDS file, which stores the password hashes within Active Directory for all of the users on a domain, according to the source. The passwords are hashed, which means a plaintext password has been processed using a one-way algorithmic function, for security reasons. In theory, hashes should be one-way only, meaning they cannot be reversed.
But the hashes in the Virgin Mobile KSA data appear to be NTLM and LM formats, which are different hashing formats that have been used by Microsoft. There are a variety of methods that can be employed to “crack” the hashes and discover the plaintext password, as penetration testing expert Péter Gombos has described.
Hunt, of Have I Been Pwned, says the value for attackers of having the NTDS file would be the potential to discover credentials for more computers or service accounts inside the organization and gain the ability to move more deeply into the network.
The source with knowledge of the incident says the attackers also planted malware written in Microsoft’s PowerShell scripting language. Attackers often use PowerShell for malicious purposes in the hope that such activity will look legitimate, because PowerShell is a built-in utility in Windows.
The source says attackers often place a web shell within the directory of Outlook Web Access, which is a public-facing directory. That move allows the attackers to remotely access a backdoor, for continuing access to the hacked network, in a manner that’s less likely to trip security alarms than many other types of backdoor access.