Application Security , Cybercrime , Cybercrime as-a-service
China-Linked APT Actors Deploying Stealthy Daxin Malware
Malware Targeted Multiple Governments in Espionage Attacks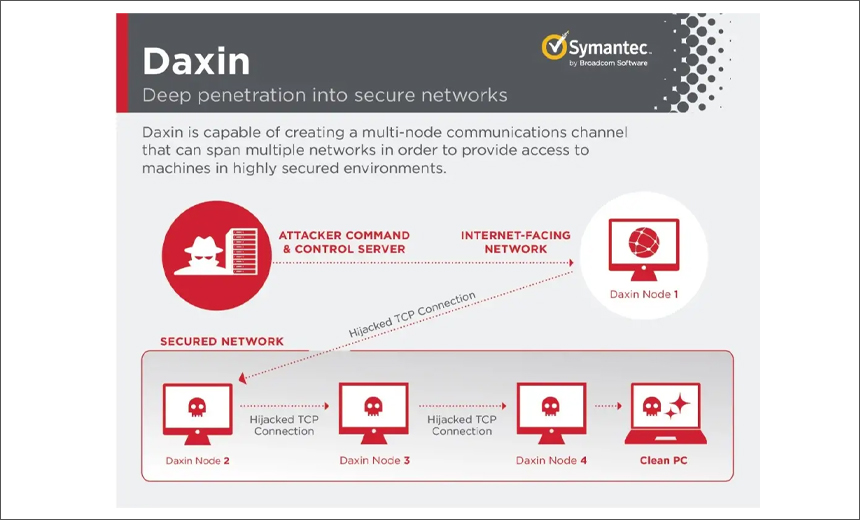
A previously undocumented advanced persistent threat campaign using malware dubbed Daxin allows attackers to run an espionage campaign aimed at entities in the transportation, telecom and manufacturing sectors that are of strategic interest to China, researchers say.
See Also: The State of Organizations' Security Posture as of Q1 2018
The Symantec Threat Hunter team, part of Broadcom Software, says it worked with the U.S. Cybersecurity and Infrastructure Security Agency's Joint Cyber Defense Collaborative to assist in detection and remediation for multiple governments targeted with Daxin malware.
"There is strong evidence to suggest the malware Backdoor.Daxin, which allows the attacker to perform various communications and data-gathering operations on the infected computer, has been used as recently as November 2021 by attackers linked to China," the researchers say.
They say they found tools associated with Chinese espionage actors on some of the computers on which Daxin was deployed.
The report by Symantec describes Daxin as one of the most advanced pieces of malware its researchers have seen used by a China-linked actor.
CISA, in an independent advisory, warns that Daxin malware is a highly sophisticated rootkit backdoor with complex, stealthy command-and-control functionality that enables remote actors to communicate with secured devices not connected directly to the internet.
"Daxin appears to be optimized for use against hardened targets, allowing the actors to deeply burrow into targeted networks and exfiltrate data without raising suspicions," CISA says.
Daxin Malware
The Symantec Threat Hunter team says Daxin comes in the form of a Windows kernel driver and calls it a rare format for malware.
The researchers say that Daxin provides advanced communications functionality, which provides stealth and permits the attackers to communicate with infected machines on a secured network without direct internet connectivity.
"These features are reminiscent of Regin, an advanced espionage tool discovered by Symantec in 2014 that others have linked to Western intelligence services," the researchers say.
The capabilities of Daxin suggest the attackers invested significant effort in developing communication techniques that can blend in unseen with normal network traffic on the target's network, the researchers say.
"The malware avoids starting its own network services. Instead, it can abuse any legitimate services already running on the infected computers," they say, adding that it does this by using network tunneling.
The Daxin backdoor can also relay its communications across a network of infected computers within the attacked organization. The researchers say that an attacker can select an arbitrary path across infected computers and send a single command that instructs these computers to establish requested connectivity.
"While the set of operations recognized by Daxin is quite narrow, its real value to attackers lies in its stealth and communications capabilities. Daxin is capable of communicating by hijacking legitimate TCP/IP connections. To do so, it monitors all incoming TCP traffic for certain patterns," the researchers say.
Whenever such patterns are detected, Daxin disconnects the legitimate recipient and takes over the connection. "It then performs a custom key exchange with the remote peer, where two sides follow complementary steps," the researchers say.
Daxin’s use of hijacked TCP connections provides stealth to its communications and establishes connectivity on networks with strict firewall rules. The backdoor may also lower the risk of discovery by SOC analysts monitoring for network anomalies, the researchers say.
The researchers also say that the built-in functionality of Daxin can be augmented by deploying additional components on the infected computer, providing a communication mechanism for such components by implementing a device named ".Tcp4".
"The malicious components can open this device to register themselves for communication. Each of the components can associate a 32-bit service identifier with the opened .Tcp4 handle. The remote attacker is then able to communicate with selected components by specifying a matching service identified when sending messages of a certain type. The driver also includes a mechanism to send back any responses," the researchers say.
Daxin's Activity
Researchers at Symantec, with the assistance of the PwC Threat Intelligence team, identified Daxin deployments in government organizations and other entities in the telecommunications, transportation and manufacturing sectors.
The most recent attack involving Daxin was traced in November 2021, but the earliest known sample of the malware dates from 2013 and included all of the advanced features seen in the most recent variants, so a large part of the codebase had already been fully developed.
"We believe that before commencing development of Daxin, the attackers were already experimenting for some time with the techniques that became part of Daxin. An older piece of malware - Backdoor.Zala (aka Exforel) - contained several common features but did not have many of Daxin’s advanced capabilities. Daxin appears to build on Zala's networking techniques, reusing a significant amount of distinctive code and even sharing certain magic constants," the researchers say.
They say the use of similar methods indicates that Daxin designers at least had access to Zala's codebase and that both malware families were used by the same actor, which became active no later than 2009.
"In a November 2019 attack against an information technology company, the attackers used a single PsExec session to first attempt to deploy Daxin before then resorting to Trojan.Owprox. Owprox is associated with the China-linked Slug (aka Owlproxy). In May 2020, malicious activity involving both Backdoor.Daxin and Trojan.Owprox occurred on a single computer belonging to another organization, a technology company," the researchers say, tying use of Chinese tools to Daxin deployment.