Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
No Coincidence: Microsoft's Timely Equation Group Fixes
Windows Exploits Dumped by Shadow Brokers Had Already Been Quietly Patched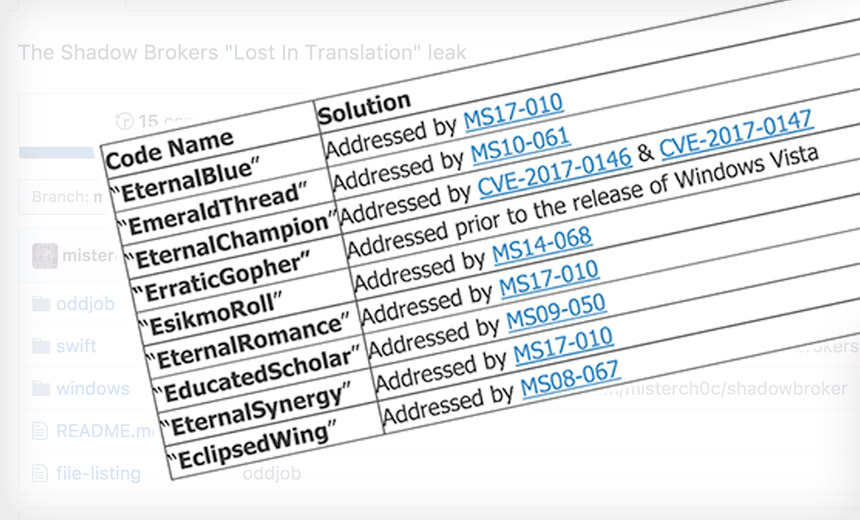
Good news for Microsoft Windows users: The Equation Group exploit tools dumped April 14 by Shadow Brokers don't work against currently supported versions of the operating system, thanks in part to patches it released in March (see Hackers Reveal Apparent NSA Targeting of SWIFT Bureaus).
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
That timing - Microsoft fixing serious flaws in its products one month before the full details of those flaws were publicly released by Shadow Brokers - probably isn't a result of luck. Instead, it's likely that Microsoft got a tip from the Equation Group, which many security researchers believe is the National Security Agency's in-house hacking team, known as Tailored Access Operations.
The rush to fix those flaws also may have led Microsoft to delay patches it was prepping to fix other critical vulnerabilities.
Meanwhile, security watchers say Shadow Brokers appears to be tied to one or more Russian intelligence agencies. The group has been timing its leaks for maximum media exposure, releasing the latest one April 14, at the start of the Easter holiday weekend.
What Chance a Coincidence?
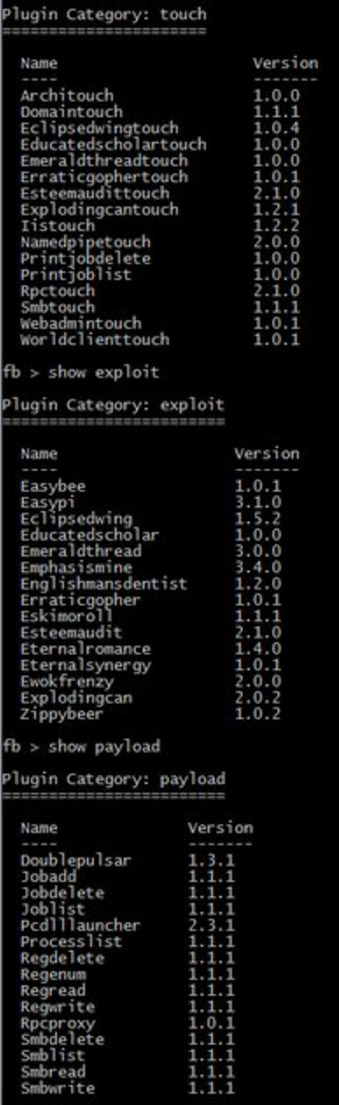
As noted by the security researchers at the Empty Wheel website, the names of many of these newly released attack tools were previewed by Shadow Brokers in January as part of a bitcoin auction for the tools, which it described as "Windows warez" - a tongue-in-cheek reference to illegally copied software. To date, however, the group has made only about $12,000 in bitcoins in related sales.
Following those attack tools being named, Microsoft in February did something unusual: It canceled its regularly scheduled monthly "Patch Tuesday" release of patches, offering only a bland explanation for the move.
Now it turns out that in its March security updates, Microsoft silently patched multiple flaws targeted by the Equation Group exploits named by Shadow Brokers.
But the exploits themselves were only publicly released by Shadow Brokers on April 14. Thus, unless Shadow Brokers privately reported the flaws to Microsoft in February - unlikely, given the group's modus operandi to date - it's more likely that someone else tipped off the U.S. technology giant.
Don't look to the patches - such MS17-010, a critical security fix for Microsoft Windows SMB Server - for answers. Unlike most fixes, Microsoft didn't credit the individual or organization that alerted it to the problem.
Queried about this missing information, a Microsoft spokeswoman tells me: "Our standard practice is to list acknowledgements on our website. We may not list an acknowledgement for reasons including reports from employees, requests for non-attribution, or if the finder doesn't follow coordinated vulnerability disclosure."
Patched: All Supported Microsoft Products
Phillip Misner, who heads Microsoft's security response team, responded to the April 14 Equation Group tool release in a blog post issued the same day. He noted that patches were already available for all currently supported Windows products.
Unfortunately, use of older, unsupported products remains widespread. Market researcher NetMarketShare reports that as of March, for example, 7.4 percent of all desktop operating systems globally were running Windows XP, which Microsoft stopped supporting in 2014.
Security researcher Efrain Torres has published a list of the recently released exploits, helpfully indexed by which current and legacy versions of Windows they target.
#ShadowBrokers Table with all the exploits leaked based on public info to help understand the impact for current and legacy unsupported OSs. pic.twitter.com/kgRD9BN83K
— Efrain Torres (@etlow) April 16, 2017
Lose the Legacy Systems
Of course, organizations that continue to use unsupported versions of Windows aren't just at risk from the Equation Group or anyone else who now possesses its exploits. That's because there's a long list of flaws that Microsoft has patched in its modern operating systems, which can be reverse-engineered and used to exploit older operating systems.
Furthermore, the attack-tool dump is a reminder that any technology a business uses might have flaws in it that are being actively and silently exploited via zero-day attacks, says security expert Haroon Meer.
Re #ShadowBrokers There are always 0-days/exploits for systems u are running. Act accordingly.
— haroon meer (@haroonmeer) April 15, 2017
Invest in Segmentation, Detection & Response
Takeaway: Don't freak out over Equation Group hacking tools. But do continue to invest in essential information security defenses - including network segmentation as well as attack detection and breach response - that can help spot, contain and remediate any attacks that may target their infrastructure.











