Endpoint Security , Forensics , Fraud Management & Cybercrime
Hello! Can You Please Enable Macros?
Mandiant Finds Attackers Phoning Victims to Advance Phishing Scams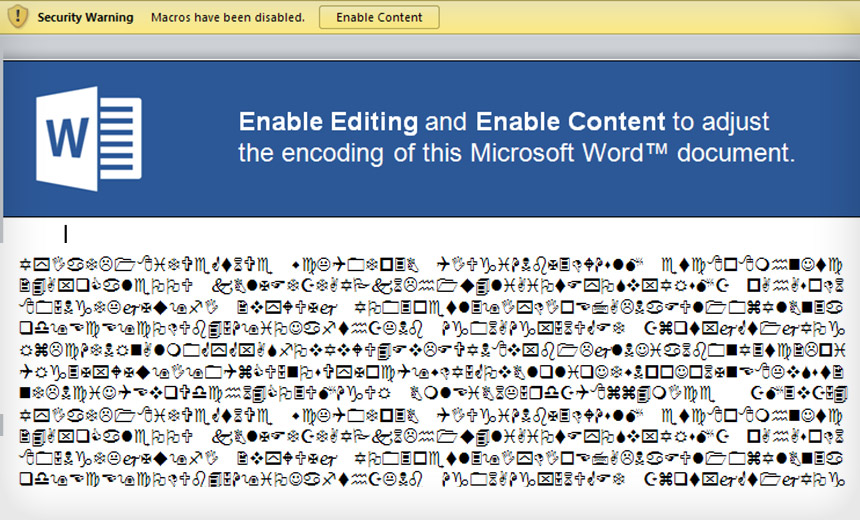
(Ring ring) Hello! I've sent you an important document over email. Can you please turn on the macros in Microsoft Office?
See Also: ISO/IEC 27001: The Cybersecurity Swiss Army Knife for Info Guardians
It may seem to be an odd phone call. And it is. But FireEye's Mandiant investigative unit says some hackers are going the extra mile when trying to compromise computers and calling victims on the phone to advance their phishing attack.
In this particular type of scam, hackers are trying to get a victim to open an Office document that has been rigged with a malicious macro. Macros are small applications that automate some functionality. But Microsoft disabled macros by default long ago in its Office applications due to the security risks they pose.
Some enterprising attackers navigate this roadblock by calling up their would-be victims and convincing them to enable macros. And in some cases they succeed, says Bryce Boland, FireEye's Asia-Pacific CTO.
"It works in a small percentage of cases," he says. "We don't have lots and lots of examples. But it only has to work against one victim in that organization, and the attacker now has a foothold."
Social engineering has long been used to trick people into divulging sensitive information or into doing something that gives an attacker an advantage. But it's not the only older technique that Mandiant saw revived in its latest attack landscape review, as detailed in its new M-Trends report released this week.
Volume Boot Record
Here's another throwback: Twenty years ago or more, boot record computer viruses were in vogue. Those involved modifying a computer's master boot record, which is the first sector of a computer's hard drive that it looks to before loading the operating system.
Over the past year, some cyberattackers have inserted remote access Trojans into the volume boot record, which is the first sector of a partitioned disk. The malicious code gets loaded before the operating system, which makes it difficult to detect, Boland says.
The attackers create a new boot entry in either the master boot record or GUID partition table. The most common modification involves creating a small hypervisor that executes and puts the machine into a guest mode before loading the OS - a feature supported by modern Intel chips, Boland says. Ironically, many security firms make the same type of modification to better detect malware.
The only way to detect the malicious modifications, however, is as they're occurring. "The attacks can completely hide themselves from the operating system environment that the user would be in," Boland says.
Oh, OAuth
Other attacks focus on OAuth tokens, which for users are very convenient, since they allow a user to grant access to one application to access data from another service without a password.
But attackers have found that such tokens are also very convenient for providing them with persistent access to targeted accounts.
Here's how: When a user sets up OAuth between two applications, an authentication token is created. Attackers, however, have cleverly created their own bogus Google applications. They send phishing emails trying to convince users to grant access to their malicious application in order to get inside email accounts or stores of shared documents.
If users do inadvertently grant access to attackers, they're in for big problems. That's because OAuth tokens live for a long time, even if someone changes their password. The functionality also bypasses two-factor authentication, which would otherwise be a tough barrier for hackers to circumvent.
"Once you've convinced a user to give authorization to an application, that victim's content is accessible directly and programmatically by an attacker completely independently of the victim's infrastructure," Boland says. "They're really just taking advantage of cloud services."
Grabbing OAuth tokens is nothing new, but it is still a problem, Boland says. The host environment will not record many of these particular types of signs that an attack has occurred, which limits any later attempts to conduct network forensics or a digital forensic review of a compromised PC.
One defensive technique against malicious OAuth token attacks is to verify which OAuth tokens have been created for an application or a cloud service, and promptly revoke any that are suspicious.
Still, that's "not something people do on a daily basis," Boland says. "Most people wouldn't think to look at it."











