Health Breaches: 20.8 Million Affected
List Grows to 464 Incidents Since September 2009
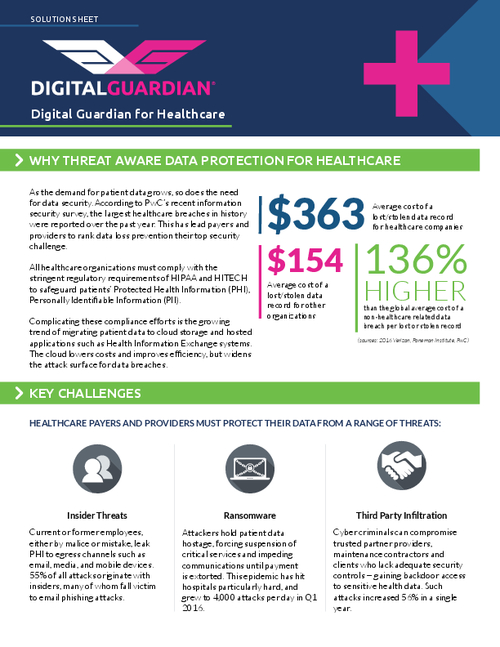
A total of 464 major U.S. health information breaches have affected 20.8 million individuals since September 2009, according to the latest federal tally, which was recently updated with 29 new incidents.
See Also: Embracing Digital Risk Protection: Take Your Threat Intelligence to the Next Level
The 29 breaches affecting 740,000 individuals were added to the tally in recent days after a lull of several weeks when no new major breaches were added to the list, compiled by the Department of Health and Human Services' Office for Civil Rights.
"This should not be interpreted as a spike. Rather, there has been a brief delay as HHS web specialists have been working on another project requiring attention," an OCR spokeswoman explains.
Among the 29 incidents added to the list are:
- The February Emory Healthcare breach involving 10 missing computer disks, which affected 315,000; and
- The April South Carolina Department of Health and Human Services breach, affecting 228,000 Medicaid recipients. That case involved a now-fired employee who was arrested for allegedly transferring patient information to his personal e-mail account.
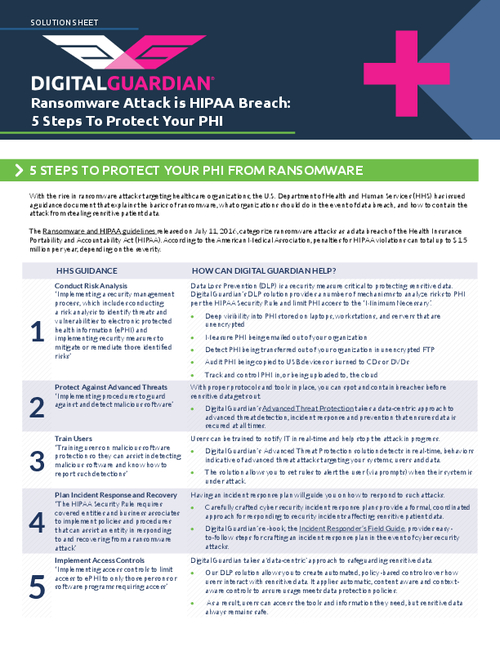
The HHS Office for Civil Rights regularly updates its tally of breaches affecting 500 or more individuals after it conducts an investigation. The list tracks breaches that have occurred since the HITECH Act-mandated breach notification rule went into effect in late September 2009.
The Breach Statistics
So far, about 54 breaches in 2012 affecting approximately 1.65 million individuals have been added to the list.
Of all the breaches reported since September 2009, 54 percent have involved the loss or theft of unencrypted computing devices or media. About 20 percent have involved business associates, although none of the 29 most recently posted breaches involved business associates.
Often there's a considerable lag time between when an organization announces a breach and when the incident makes it to the OCR list, because of the need to confirm the details. And OCR may take as long as two years to announce enforcement action, such as resolution agreements, as a result of a breach.
For instance, an October 2009 breach involving a stolen USB drive at the Alaska Department of Health and Social Services triggered a lengthy investigation of the agency's security policies and eventually resulted in a settlement that was announced last month (see: Alaska Breach: Tip of Iceberg).
OCR's breach investigation led to the discovery various HIPAA non-compliance issues at the Alaska agency, including a lack of timely risk assessments and staff training. Under a resolution agreement, the agency agreed to pay $1.7 million and carry out a corrective action plan.
Susan McAndrew, OCR's deputy director of health information privacy, says detailed resolution agreements "draw attention of individuals to problem areas," and, as a result, help others learn lessons that can be applied to prevent other breaches. The Alaska case, for example, highlights the importance of updating risk assessments.