Governance & Risk Management , Next-Generation Technologies & Secure Development
Researcher Unleashes Ransomware on Tech-Support Scammers
Fun Factor Aside, 'Hacking Back' Carries Legal Risks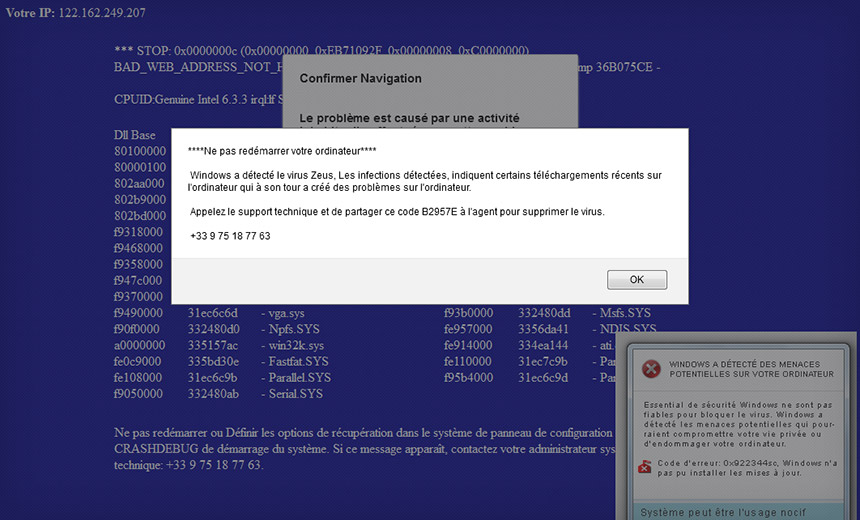
Who doesn't hate tech-support scammers?
See Also: The Cybersecurity Swiss Army Knife for Info Guardians: ISO/IEC 27001
Thanks to French security researcher and malware analyst Ivan Kwiatkowski, however, we can share in some tech-support scammer one-upmanship.
After Kwiatkowski's parents stumbled onto a tech-support scam website, he says that he ultimately retaliated by tricking one of the site's supposed tech-support agents into executing a Locky ransomware installer on his system.
Kwiatkowski says in a blog post that his parents, in France, recently got a new computer and were online for all of 30 minutes before stumbling across a site that warned them that their PC was infected with the Zeus virus that Windows couldn't fix. The site advised them to immediately contact a listed telephone number, which began with a French country code. Instead, they phoned their son, who warned them away.
My parents have had a new computer for 30 minutes and have already stumbled upon an online scam. I can't even. https://t.co/9eMRpf3y6z
— Ivan Kwiatkowski (@JusticeRage) August 2, 2016
The Usual Smoke and Mirrors
Kwiatkowski then opted to fire up a Windows XP virtual machine and reached out to the "tech support" team, getting a woman named Patricia on the phone who instructed him to install a remote-support client that she then used to access his system. Without recognizing the VM environment, and while sticking closely to a French-language script, he says Patricia then typed in a number of commands to make it appear as if his system was infected with a virus.
Kwiatkowski says he played along, capturing screenshots along the way. After claiming that his 15 minutes of free tech support time were up, Patricia said he needed to buy an anti-virus program priced at $189.90. "Before I have the opportunity to get my credit card, she goes back to the terminal, runs netstat and tells me that there's someone connected to my machine at this very moment."
Kwiatkowski says he replied: "Isn't that you? ... This says it's someone from Delhi."
Eventually, Kwiatkowski begged off, but he called back again 30 minutes later after realizing that some of his screenshots didn't work.
This time, his call was answered by "Dileep," who said he needed a €299.99 ($338) "tech protection subscription."
"In the meantime, I hear other operators in the background repeating credit card numbers and CVVs aloud," Kwiatkowski says. At that point, he opted to retrieve a JavaScript Locky installer from his email junk folder, which he uploaded via the remote-support client, telling the agent: "I took a photo of my credit card, why don't you input the numbers yourself?"
Kwiatkowski says he hopes, but doesn't know for sure, that the scammer's system - and every other system to which it connected via the local area network - was then forcibly encrypted by the ransomware.
Don't Try This at Home
Kwiatkowski doesn't advocate this course of action for other potential tech-support victims. But he does urge everyone to waste scammers' time by keeping them engaged in meaningless phone chatter for 15 minutes, thus taking a bite out of their profits.
To be clear, phoning scammers is one thing. But security experts have long warned that individuals - or nation-states - that attempt to "hack back" may face serious repercussions. "There's a lot of talk around hacking back - and while it may be very tempting, I think it should be avoided to stay on the right side of the law," University of Surrey computer science professor Alan Woodward tells the BBC.
"But wasting their time on the phone I have no problem with," adds Woodward, who's also a cybersecurity adviser to the EU's law enforcement intelligence agency, Europol. "I even do that myself!"
Support for Tech Support Scam Victims
Kwiatkowski's story is a reminder that while fake tech-support gangs' claims might seem outlandish, less technically savvy PC users sometimes fall for them.
@nevali a friend had someone allegedly from Microsoft threaten to blow up his computer.
— badly drawn bee (@soapachu) August 17, 2016
Based on stories I've written about fake tech-support gangs, many victims have reached out, asking me if they've been scammed and what they can do about it. The short answer: File a fraud report with your credit card company. Also report the attempted fraud to relevant authorities, such as the FBI's Internet Complaint Center or to the U.K.'s ActionFraud.
Doing so helps authorities track these scams and hopefully disrupt them - no ransomware "hacking back" required.











